Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Next step...
Not to mention the entry node will see your IP address, so if it’s compromised, a hacker...
Suppose cybercriminals can access the login information of one of your online accounts. In that case, they...
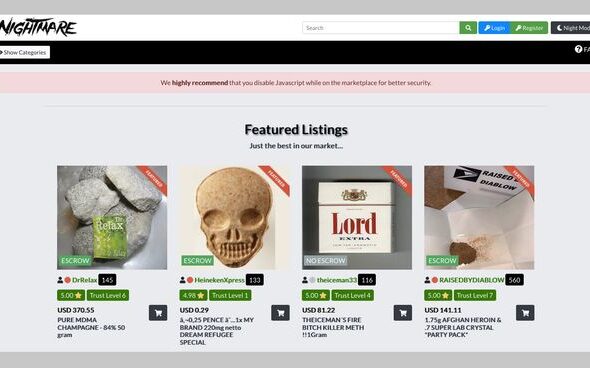
When regulators cracked down in the 2000s, many addicted users turned to heroin. Heroin became a major...
We evaluated our method on our annotated data set, which yields an accuracy of over 90% for...
You can also raise queries and make complaints via its 24/7 customer service. In short, using a...
Ulbricht was also charged with a murder for hire plot and was sentenced to a double life...
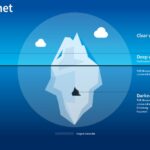
That means that only 0.024% of all the known pages are findable in Google’s search engine. The...
As mentioned before, your ISP and government institutions are not able to see what sites you visit...
These allow you to create a virtual OS within which you can access the Dark Web safely....