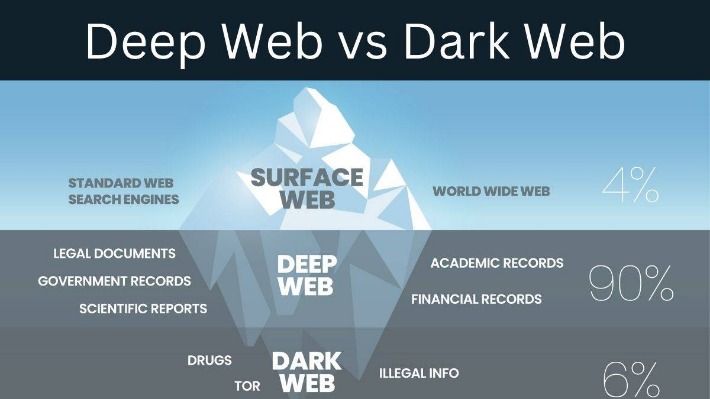
It is a network where users can remain anonymous and engage in various activities, including the exchange of cryptocurrencies. While the Dark Web has gained notoriety for its association with illegal activities, it is important to note that not all activities conducted on the Dark Web are illegal. Within the realm of cryptocurrencies, the Dark Web has become a platform for people involved in crypto to engage in transactions and exchange information. Our results also support recent recommendations of paying attention to individual sellers rather than entire DWMs40. Law enforcement agencies, however, have only recently started targeting individual sellers.
What Makes Deepvue Different From Other Stock Research Tools?
This makes it even harder for third parties to see your email traffic. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. The BBC news website has a special .onion site, which you need to access via the dark web. Its goal is to offer anonymous access to the content without being censored, no matter where you live.
Real-World Applications Of The Tor Network
The importing process via MT4 file is extremely easy and the automated charts with entries are amazing. The whole process is extremely easy and helps to keep me accountable for my trading by having a professional system to manage my business. The platform is very comprehensive and takes a bit of time to get used to, but they have many videos on their YouTube to help with this as well as their support team. TradesViz is the most useful trading journal on the market for finding and quantifying your edge. One of the main advantages of Tor Forex is the ability to bypass strict regulations and restrictions imposed by financial authorities. In many countries, Forex trading is heavily regulated, requiring traders to provide identification, proof of address, and adhere to certain capital requirements.
Risk Factors
That’s why we dug into 20+ of the most popular platforms, rating them on everything from fees and features to education and support. With so many online brokers out there, finding the right one can feel overwhelming—whether you’re just getting started or already deep in the markets. We have simplified the cybersecurity assessment process and made it accessible for all businesses. To learn more about how Cybernod can help protect your business and stay ahead of cyber threats, visit our website at Cybernod. Secure your organization’s future by partnering with a trusted leader in cybersecurity solutions. For further reading on privacy tools and whistleblowing platforms, visit SecureDrop’s official site.
“What-if” Scenario Analysis

To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. And, of course, think twice before sharing too much personal details online. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password.
How The Silk Road Functioned As An Online Marketplace
Despite the significant growth of Darkweb usage and its potential impact on multiple SDGs, there needs to be a more systematic analysis of its alignment with various SDGs. Dark web monitoring and threat intelligence firms like Cyble help mitigate these risks with advanced AI-driven threat intelligence solutions. Cyble’s platforms, such as Cyble Vision, monitor the dark web for emerging threats, providing real-time insights to protect organizations from cybercrime. By leveraging such tools, businesses and governments can protect their data and communities from cyber actors. Similarly, threat intelligence is another tool that involves the collection and analysis of data about potential or existing cyber threats to help organizations understand and prepare for future risks. This can include gathering information from various sources, including dark web forums, and analyzing trends related to cybercrime.
The Legality Of Accessing The Dark Web
The S2S network is mostly populated by U2U-only sellers, followed by market-only, and market-U2U (see Supplementary Information Section S5). It may be too late for this case to make much of a difference as a deterrent. According to new research from security firm Recorded Future, insider trading activity on the dark web peaked a few years ago, and fizzled out after 2018. That year, popular Tor-based site The Stock Insiders shuttered in August, followed a few months later by multipurpose hacking forum Kickass Market.
Collective Dynamics Of Dark Web Marketplaces
Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously.

Copyright © 2025 FactSet Research Systems Inc.© 2025 TradingView, Inc. By implementing these recommendations, policymakers and law enforcement agencies can take steps to mitigate the challenges posed by the Darkweb and protect the public from its potential harm. The Scopus database 36 was used to find published articles on Darkweb. The rationale behind choosing the Scopus database for sourcing bibliographic data in this study primarily rests on its capacity to meet stringent quality standards for indexation. Moreover, Scopus enjoys popularity due to its comprehensive coverage, encompassing a wide spectrum of journals spanning diverse subject areas. It’s worth noting that Scopus stands out as the foremost citation and abstract database and serves as the most widely employed search 30,37,38.
Overall, Abacus Market distinguishes itself through rigorous security measures, effective moderation policies, and a strong emphasis on protecting user privacy. Despite minor accessibility inconveniences, these strengths have solidified its position among the top dark-web marketplaces in 2025. Stock market trading, Forex trading, “knowing what is happening before the rest” news exchanges and commodity sales all take place in the forum. Over the past two years, the researchers have monitored roughly five posts a week and over $32,000 in transactions, all of which are made in Bitcoin.
Best Online Brokers And Trading Platforms Of 2025
This trove of stolen data included names, addresses, Social Security numbers, and phone numbers, leaving millions of individuals vulnerable to identity theft. Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million. The main complaints against SogoTrade have to do with its trading platforms, which some customers find cumbersome and lacking in advanced features. Some users also note a poor user experience when it comes to research. However, positives include an easy account-opening process and multilingual customer support.
- Our findings suggest that DWMs are much more than mere marketplaces39.
- Traditional Forex brokers are required to be licensed and regulated by financial authorities, ensuring the safety of client funds.
- Stock market trading, Forex trading, “knowing what is happening before the rest” news exchanges and commodity sales all take place in the forum.
- Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data.
- Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
- Shortly after the breach, a hacker group known as USDoD listed this data on dark web marketplaces, pricing it at a staggering $3.5 million.
Eventually, the system collapses, and most people lose their entire investment. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for. Others sell pirated eBooks, academic materials, and entire premium courses ripped straight from paid platforms.
In fact, when we compute the total net income for each seller, a considerable fraction (16%) has a negative net income because they spend in markets where they are not classified as sellers, or in the U2U network. Moreover, we find a change of trend between the seller and the buyer median net income time series which reflects the dominance of markets, as detailed in the next section. However, owing to the difficulty of identifying relevant transactions, most studies rely on user surveys17,18 and data scraped from DWM websites19,20,21,22,23,24. In particular, these studies are based on user reviews which carry many inaccuracies, for instance, with respect to the time and value of the transaction19, that further compound error in other measures. Moreover, data scraped from the DWMs cannot assess the U2U transactions which account for the largest fraction of the total trading volume of the ecosystem13.