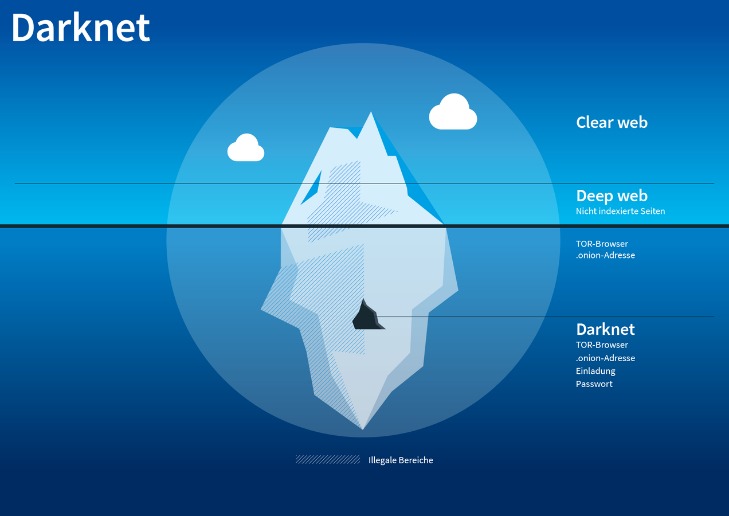
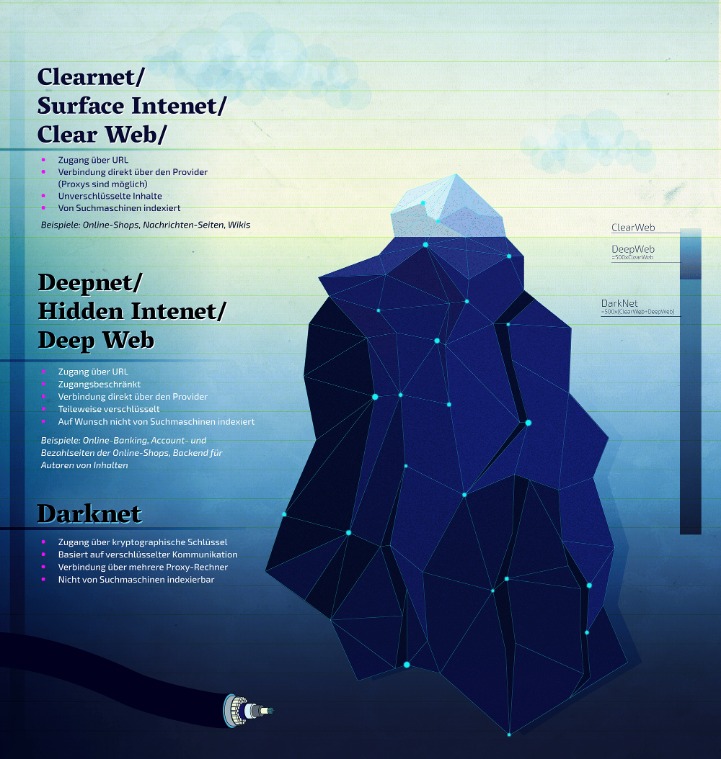
From a philosophical perspective, individuals who rely on fake documents for personal gain compromise their own integrity, fostering personal moral ambiguity that can permeate other areas of their lives. The choice to utilize a fake ID reflects broader questions of personal ethics, signaling a willingness to place immediate desires or convenience over long-term responsibility and social accountability. Law enforcement officers conducting routine traffic stops, public event checks, or investigations often detect counterfeit IDs through portable scanners and specialized software. Officers are trained to recognize physical inconsistencies like poor printing quality, incorrect fonts, mismatched data, or suspicious behavior. Additionally, verification against national databases can instantly identify fraudulent documents, resulting in immediate arrest or further investigation. The Dark Web refers specifically to websites and services hosted inside Darknets.
If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. On the dark web, even a minor slip-up can cause you big consequences.
At Digital One Agency, we’re here to help you build legitimate, secure, and profitable tech ventures — the kind that scale, attract real customers, and don’t end with handcuffs or disappearing acts. Darknet traders don’t want full decentralisation — they want convenient anonymity with dispute resolution. That’s hard to get without some form of centralisation, which always becomes a target. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. The second category consists of data stores, which specialize in stolen information.
2020 saw a massive increase in cyberattacks, according to PA, not only in quantity, but the variety of items to purchase has grown as well, such as hacked crypto accounts, web services like Uber accounts and face images. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats. Ethically, they must minimize harm, responsibly handle any stolen or sensitive data (often notifying victims or law enforcement), avoid entrapment, and maintain research integrity. Internet criminals buy and sell personal data on the dark web to commit fraud. Here’s a breakdown of what your personal details might go for on underground marketplaces, according to the Dark Web Price Index by Privacy Affairs.
Russian Market has consistently remained one of the most popular and valuable data stores on the dark web. Its affordability and reliability have earned it a loyal customer base. The platform’s activity has increased significantly over the past year, indicating its growing influence and market share in the underground economy. We’re world-class at cybersecurity, AI, and blockchain applications.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
In fact, many openly advertise their services on darknet forums. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. Some services even target entire companies or public systems. But somewhere between production and purchasing, things can get dirty. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade.
Mobile Store – Buy Apple And Samsung Phones With BTC
Despite these takedowns, modern illegal markets have evolved by adopting decentralized hosting structures and integrating privacy-focused cryptocurrencies such as Monero to eliminate traceability. Hydra, a Russian-language Dark Web marketplace, operated for years before its 2022 takedown by German authorities, demonstrating the adaptability of these underground economies. Flash BTC Software allows you to send BTC fakes on the blockchain network. These Bitcoins can stay in the wallet for 600 days maximum before being rejected by blockchain and finally displayed as unconfirmed in the wallet.
Your Identity May Be At Risk Of Being Stolen And Sold On The Dark Web
Because there are no passwords, your username also acts as your password. To check your e-mail, you simply enter your username, e.g. , and you’re logged in. It’s important to ensure you select a hard-to-guess username so others can’t access your mailbox.
Shifts In User Behavior And Marketplace Structures
The hacker group Play, which was responsible for the attack, had captured 900 gigabytes of data. As Xplain did not respond to the ransom demand, the data was published on the darknet. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation.
- Therefore, you must know how to access dark web marketplaces safely (covered later in this article).
- They charge 5% service fee for all orders placed on market and 1% transection fee for all outgoing transections.
- They use these, for example, to sell illegal goods, whereby the traces initially lead to the actual owner of the hacked account, while the perpetrators remain hidden.
- You can find a lot of goods and services packed with stealth high-level encryption, no JavaScript, and anti-DDoS protection.
- People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware.
Dark Web Carding Store Links
Many of the credentials advertised for sale on the dark web are genuine — meaning they were stolen from a bona fide citizen and illegally sold to a new identity seeker. Following Silk Road’s closure, AlphaBay emerged in 2014, introducing advanced security features such as two-factor authentication and multi-signature escrow services to improve vendor credibility. At its peak, AlphaBay had over 400,000 users and facilitated transactions exceeding $1 billion.

Law Enforcement Takedown

Fake IDs and forged documents—ranging from driver’s licenses to passports—are increasingly accessible through the shadowy networks of the dark web, a hidden segment of the internet accessible only with specialized tools like Tor. This underground marketplace thrives on anonymity and cryptocurrency transactions, making it particularly attractive for those seeking to conceal their identities or bypass legal restrictions. Despite their allure, these fraudulent documents come with substantial risks, both legally and personally. Understanding how fake documents originate, why they are popular, and the severe consequences of their use is essential to navigating and safeguarding oneself in today’s digital landscape.
DeepMarket is another one of these dark web sites that sell everything your local vendor won’t or can’t sell to you. Does offer basic vendor-transparency, the vendor’s previous history can be verified. For security, 2-Factor authentication can be enabled via PGP. A mnemonic code, as well as a security PIN too can be set. This market specialized in selling marijuana related products and magic mushrooms, with no “hard drugs” for sale.
Is Claude Safe And Secure In 2025?
I keep updating this collection time to time with active deep web links. If you are looking for dark web sites which offer hacking services, below .onion sites are for you. Accounts are listed with country, account type, balance, price and order link. It is operated by a group of skilled individuals from different countries across the globe.

Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes. Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty. It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online.
The users on this site can review and rate the products that promote reliable and fraudster vendors. Organisations should follow industry standards on securing data and implement security technologies to prevent cyber attacks and reduce the risk of data being stolen and traded in the darknet markets. Palo Alto Networks Next-Generation security platform provides a holistic solution to protect the digital way of life by safely enabling applications and preventing known and unknown threats across the network, cloud and endpoints. For more information on the next-generation security platform visit here.