PIA is popular in the USA because it offers servers in all 51 states. People in the United States and abroad can use it to venture into the dark web in privacy. With RAM-based servers in 90+ countries and features like WireGuard, IPv6 leak protection, and a kill switch, worries are over. Like NordVPN, this provider doesn’t store logs and has around 20 third-party audits to prove it.
Step 5: Find Verified Onion Links
Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. If you’re lucky enough, you can find it on clearnet privacy forums. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. It will offer you an additional layer of encryption to access the deep parts of the internet.
What Is The Dark Web? How To Use Tor To Access The Dark Web
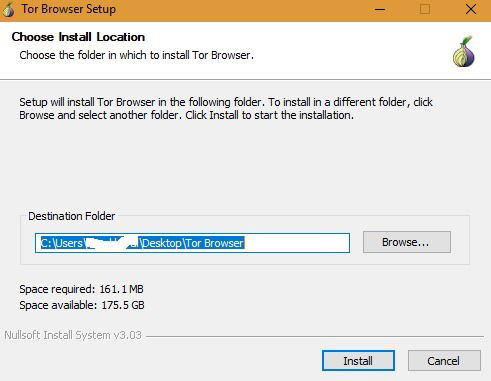
However, even these resources are not immune to compromise or the inclusion of malicious links, so a degree of skepticism is always warranted. Finally, users whose internet connection relies on a proxy server can configure these settings within the “Configure Connection” window as well. This typically involves entering the proxy type, address, and port, and potentially authentication details if required by the proxy server. In most home network setups, proxy configuration within Tor Browser is not necessary, as the browser is designed to route traffic through the Tor network independently.
Matthew has written for companies in diverse industries, including emerging technologies, wellness, consumer apps, enterprise software, UI/UX, outsourcing, and education. In combination with that data, and data gathered by other methods and/or tactics may in fact lead to complete exposure and could eventually lead to the police standing at your doorstep. You can either sell or buy goods on the dark web, but both present difficulties. If you want to prevent getting infected on the dark web, keep your Tor browser updated to the latest version available, disable JavaScript, Flash and other plug-ins, and use common sense. The dark web is also a place for scammers to attract vulnerable and unwitting victims.
- Instead, sites have complex .onion addresses, making them difficult to find without the exact URL.
- These sites are only accessible over the Tor network and are commonly used for privacy and anonymity.
- Note you should use a separate browser than the one you normally use to help ensure anonymity.
- This means you should never change the default settings in the Tor Browser.
- DarkWeb “marketplaces” guarantee confidentiality and anti-surveillance for your online purchases that you simply won’t find on any other websites.
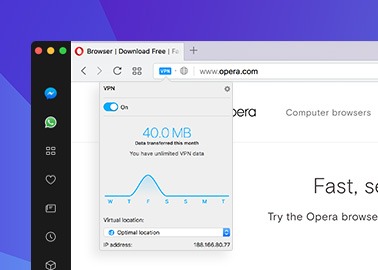
Use A VPN To Stay Safer On The Dark Web
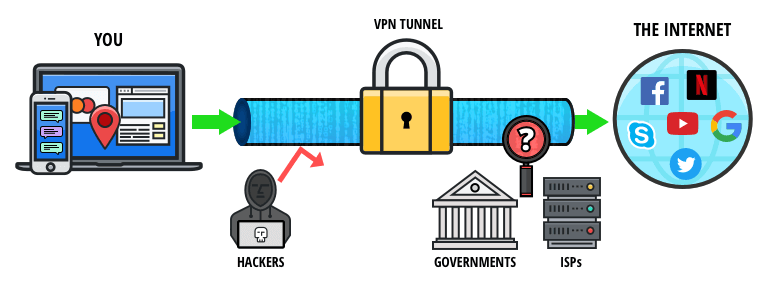
Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network. Internet providers and websites can detect when Tor is being used because Tor node IPs are public. Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used.

Many major companies have reserved .onion domains and host websites there, and there is a list of onion services on Wikipedia. The Deep Web forms a more expansive but hidden layer beyond the reach of conventional search engines. This section comprises content requiring specific permissions, login credentials, or specialized tools for access. Examples include password-protected websites, private databases, and subscription-based resources, contributing to a broader yet less visible realm on the internet.
- This was also Google’s latest official update on how many pages are in their database.
- This includes avoiding logging into any personal accounts (social media, email, banking, etc.) while using Tor Browser.
- Unlike the surface web, where search engines like Google and Bing index vast amounts of content, onion services are generally not indexed by traditional search engines.
- These groups include Mazafaka, Trojanforge, hack forum, xDedic, and dark0de.
Essential Safety Tips To Minimize Risks
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. In short, even with Tor, there’s no perfect anonymity online, but there are efforts to claw back our power online, says Lewis. Using the Tor browser is simple, but knowing when to fire it up is more complicated. Another challenge is CAPTCHAs; because Tor behaves differently than other browsers, it’s more likely to trigger the bot-hunting system, so be prepared to face more of them than usual.
Why You Need A VPN To Be Safe On The Dark Web
Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. For several years, Yahoo was at the apex as the internet’s best web service provider, offering… To provide anonymity, Tor is generally quite effective, but not completely foolproof. If the person tracking you is very advanced and has unlimited resources, they could conceivably de-anonymize you when you make certain mistakes, like downloading files or enabling scripts.
This prevents data from leaking between applications and makes your Internet traffic more secure. Your download and upload speeds may be slower, but that is the tradeoff for secure Internet browsing. This means you can use your favorite browser instead of the Tor Browser and still benefit from being routed through the Onion Network. This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. Because of the relaying of data through the onion nodes, and the encrypting and decrypting taking place at each node, your internet connection will slow considerably.
Well known for its emphasis on security and privacy, the Tor browser distinguishes itself from mainstream browsers like Firefox or Chrome. Unlike the direct route taken by conventional browsers, Tor employs a series of encrypted servers known as nodes, chosen randomly, to ensure both user and site anonymity. Law enforcement agencies worldwide have grappled with the challenges posed by the Dark Web, attempting to balance the need for online privacy with the necessity of combating criminal activities. If you are looking to read combating crime on the dark web online, many resources and platforms are available that shed light on the ongoing efforts to curb the growing threats of cybercrime. Like the regular surface web, the dark web offers its own social media sites and web forums.
Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together. Once you have those, there are several ways to tunnel through the dark web.
Swap Data In Countries That Censor The Internet
The Tor browser is designed to provide improved online anonymity and security. However, be careful when using the Tor Browser to access the dark web. The dark web is a dangerous place, and all bets are off on your safety. The exit node removes the final layer of encryption on your data.
This means the Tor Browser is not recommended for streaming video, playing games, or downloading large files. These sites are only accessible over the Tor network and are commonly used for privacy and anonymity. The Tor Browser also features many built-in protections that protect against tracking and fingerprinting. Exploring the dark web can be a fascinating journey, but it requires the right tools and safety precautions. From popular options like Tor to specialized environments like Whonix and Tails, each dark web browser offers unique features to enhance your privacy and security. The core principle of the Tor network was first developed by U.S.
While there are numerous VPN services that work well with Tor, I’ve found that NordVPN offers the best protection and compatibility, and keeps your personal information safe. This ensures that your real IP address is hidden from the first Tor relay (it sees the IP address that your VPN provider supplies). Then the Tor anonymity network relays further obfuscate your true location, as the browser relays your browser traffic through several relay locations.
Do I Need A VPN To Access The Dark Web?
The Tor Project also offers the Tails operating system for users who prefer a complete privacy solution for accessing the dark web safely. DuckDuckGo offers an .onion version of its search engine, while Sci-Hub offers access to millions of scientific articles and papers. Library Genesis offers a search engine for collections of books on such topics as computers, business, technology, and more. These are only a few of the .onion search engines that are available. Tails is a portable, live operating system that offers high-level privacy with built-in dark web access.