As the name suggests, Impreza Hosting is a (dark) web hosting service that provides all sorts of goodies such as domain names, host email services, and even servers for rent. A little refresher on the dark web – it’s like a gathering house, where all sorts of people congregate. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download.
With so many threat and APT groups actively using Telegram, the platform becomes a vital source of information. The various channels focus on stealer logs, combo lists, scam lists, and a community marketplace. Moon Cloud serves as a hub for data obtained from stealer logs – mainly LummaC2 or Redline. The data shared on this channel includes compromised credentials such as email addresses, IP addresses, passwords, user names, etc.
Is It Legal To Browse The Dark Web?
- Some visitors simply enjoy the anonymity and might just join an online chess club there or Blackbook, the social networking site exclusively for the dark web.
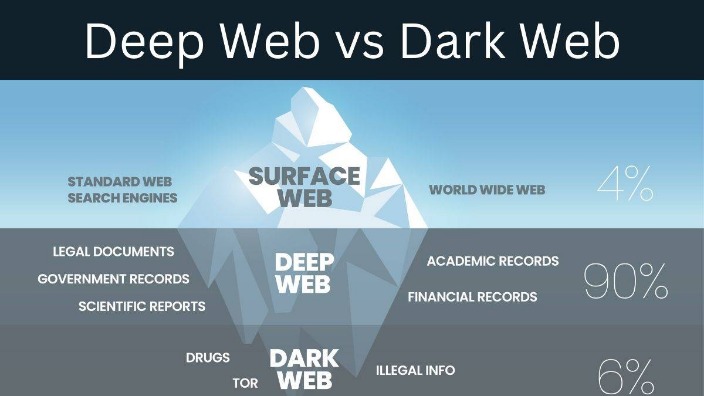
- To search for the onion URLs, you need access to a deep web search engine.
- Many dark web search engines are available, and no single option is objectively the best.
- Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy.
- Using Tails OS can further security, as all your data is reset every time you close the device.
On the downside, web surfing on Tor can be slow since your traffic is traveling over the various network nodes. By staying alert, verifying sources carefully, and consistently practicing good security habits, you significantly reduce the risk of encountering threats or compromising your security. While exploring the dark web can offer valuable privacy benefits, it’s crucial to understand common risks and how to manage them effectively. Sorry, a shareable link is not currently available for this article. Much like a regular business, the typical darknet CSAM forum is hierarchically organized, and different forum roles are distinguished (see Fig. 4; van der Bruggen and Blokland 2021b).
How To Access The Deep Web?
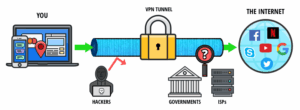
Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites.
What Kind Of Illegal Activities Are Commonly Found On Telegram Channels?

Although not a deep web search engine in the traditional sense, WorldCat can help users uncover academic and research materials that may not be accessible through standard search engines. Wikipedia’s deep web version is a directory of websites on the Tor network. One can access the directory of different onion websites by visiting its official website. Although you might need the Tor browser to visit some of the onion pages. So while it’s not a typical deep web search engine, it can be used to uncover content that has been removed or altered on the surface web. mark it means it has been verified as a scam service and it should be avoided. If the website you are trying to visit has Recommended mark it means it has been verified and is safe to use. In addition to this, the anonymity provided by the dark web makes it very easy for a website to distribute malware or disappear with any payments you made to it without fear of consequence. Protect your business with end-to-end encryption and compliance-ready security. Transact Bitcoin privately with an encrypted self-custody wallet.|Users can ask questions, share answers, and engage in discussions without revealing their identities. Riseup provides email and chat services that keep no record of your online activity. Thankfully, with the right guide — and a tool like a VPN (Virtual Private Network) by your side — you can navigate these hidden sites safely without falling victim to any hazards along the way. Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week. In addition, it also revisits already indexed sites to update discover and remove downed and offline sites. However, to maintain the servers, they offer the possibility of inserting advertising banners on their home page.}
WANT TO TRY THE TOP VPN RISK FREE?
It offers outstanding privacy features and there is currently a discounted rate available through this link. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful.
The Deep Web refers to web data you can’t find using a search engine like Google. Unlike the Dark Web, the hidden corner of the internet often used to conduct illicit or anonymous activity, anyone can get to the Deep Web safely using a regular browser. We’ll show you how to find information on the Deep Web and safely dip your toes into the Dark Web. The darknet is a part of the internet that is not indexed by conventional search engines, often requiring specific software and configurations to access. It is a place where anonymity and privacy are highly valued, making it a frequent point of interest for researchers, privacy advocates, and individuals concerned about online security.
Can You Access The Dark Web With A VPN?
Facebook’s official dark web version helps users access the platform in countries where it’s blocked. During testing, I confirmed it provides the same functionality as the regular site while adding Tor’s privacy benefits. The interface works smoothly, but it usually loads slower due to Tor routing. Proton Mail’s dark web version provides end-to-end encrypted email with enhanced privacy protection.
Never Share Personal Information

But beyond the deep web lies a host of hidden dangers that parents should be aware of – the darknet. The darknet provides a haven for those who want to go unnoticed, including those who are keen to break laws. The anonymity provided by the darknet challenges LEAs in identifying both victims and perpetrators. The sheer number and size of CSAM forums active on the darknet forces LEAs to prioritize and allocate their available resources to those individuals who are deemed to pose the highest risk.

Teens And The Darknet
If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks.
The Drug Users Bible
Teens can easily access the darknet and if they do they risk entering into a world of porn, drugs, fake ids, guns, and many other hidden dangers. This part of the Internet is a portal into a world in which identity ceases to exist. An alternative to Tor is to use a paid VPN service, which can also prevent ISPs from monitoring what sites you’re visiting. It can do this by creating an encrypted internet connection with a server run by the VPN provider. Back in 2018, Pornhub jumped on the bandwagon by introducing its own product, VPNhub. With these guidelines, exploring the dark web can be done securely and confidently.
Many countries lack the equivalent of the United States’ First Amendment. Darknets grant everyone the power to speak freely without fear of censorship or persecution. That said, three common Onionland starting points are The Hidden Wiki, TorDir, and TorLinks. All the directories in Onionland always point to Torch as a search engine of onions, but it never works properly.