In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related. Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings.
One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences. The unique part is that the platform offers free samples of stolen information, often to attract more customers. STYX market features a robust verification process, making it look more exclusive.
- For compliance teams, this case highlights the importance of continuous monitoring, real-time intelligence, and robust risk mitigation strategies.
- While it received a relatively small share of large retail purchases as shown in the previous chart, Abacus Market is one such example.
- The reliable relationship between vendors and customers was mirrored in customer feedback on vendor reliability which often manifested in users declaring themselves as repeat customers (T4).
- Min-max scaling is a normalization technique commonly used in data preprocessing to transform numeric variables into a specific range, typically 0, 1 (66).
- Monero, in particular, has become the preferred cryptocurrency on the dark web in 2025 due to its advanced privacy mechanisms, which obscure transaction histories and wallet balances from public view.
The Chainalysis 2024 Crypto Crime Report
When it comes to finding alternative platforms in the dark web marketplaces, there is no shortage of choices. Law enforcement strategies are crucial in combating cybercrime and protecting individuals and businesses from malicious activities on the darknet. By working together, law enforcement agencies and private entities can share information, resources, and expertise to effectively investigate and prosecute cybercriminals. Explore the vast array of illegal goods and services available on darknet markets, where you can stumble upon a world filled with unimaginable offerings.

Access Our Coverage Of TRON, Solana And 23 Other Blockchains
While some of these markets were shuttered by law enforcement agencies – some took the easy way out with exit scams. Here are some of the now-defunct dark web markets that were notorious for cybercrime. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews.
Years Of Rapid Security Assessments
It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity. Torzon Market showed up on the dark web in September 2022, and it’s been growing steadily ever since. These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services.
Problematizing Content Moderation By Social Media Platforms And Its Impact On Digital Harm Reduction
It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. Governments and businesses must invest in advanced threat intelligence, cyber defense, and counter-espionage measures.
Darknet Market Vendors Turn To DeFi
By placing more test orders with him and observing his online and offline behavior, they were able to intercept more of his packages and build their case further. While police had managed to seize some of his shipments to customers that were flagged by PostNord, Denmark’s main private mail carrier, they’d yet to uncover his real world identity. Malvax ran a sophisticated operation, relying on mixers and other obfuscation techniques to protect his identity.
The anonymity provided by the darknet makes it incredibly challenging to gather concrete evidence that can lead to successful prosecutions. Additionally, the constantly evolving nature of technology requires law enforcement agencies to constantly adapt their strategies and stay one step ahead of cybercriminals. Brace yourself, because we’re about to take you on a journey through the perilous world of darknet markets. Customer reviews found on the Abacus site indicate that some of its American vendors sell drug products laced with fentanyl. Throughout the history of the darknet market ecosystem, at different turns one marketplace has typically played the dominant role.
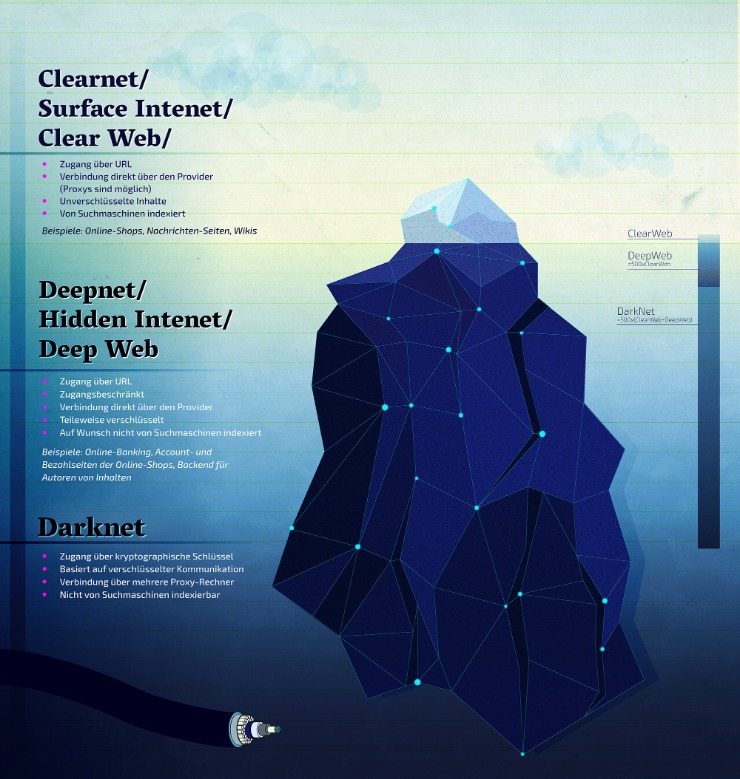
Cypher Marketplace
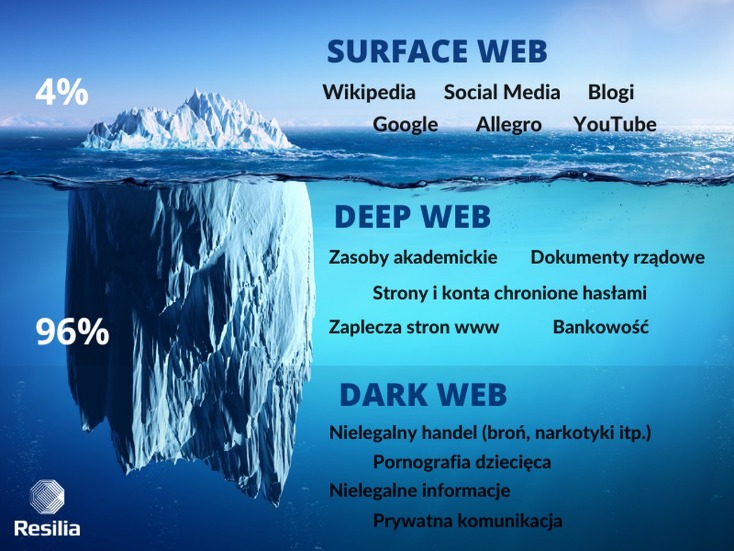
The darknet marketplace is home to a plethora of illegal and legal activities. However, the markets are dominated by things like illegal drugs, explicit content, pirated files, hacking services, and stolen personal information, among others. The darknet markets are a hotbed for selling stolen personal information. The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. While there are legitimate products and services in the darknet markets, often, these markets deal with illicit goods and services like drugs, fake documents, and hacking services. Their presence can make you wonder why darknet markets and not just the regular online stores.
Similarly, the lifespan of criminal actors on online carding forums, particularly in the form of’long-term participation in the market,’ has been identified as an indicator of trust 29, 144. Prior research also identified the length of time vendors are active on the sites as a signal of trust 33, showing that seniority is significantly and positively correlated with criminal opportunity. This suggests that longer engagement may improve criminal performance, which indicates reliability. It is, therefore, reasonable to hypothesise that the longer sellers have been in the market, the lower the probability or number of fraud cases. Darknet markets commonly display the seller’s registration date, as Alphabay market proves (S1 Fig). Activities on dark-web marketplaces are closely monitored by international law enforcement agencies.
Most darknet markets indicate the date the sellers started selling on the market. Alphabay market contains this information, as you can see in the attachment. As Axelrod 57 show, the shadow of the future has an impact on increasing trust and deterring opportunistic behaviour. While theory allows for the emergence of cooperation in infinitely repeated games, defeat in finite repetitions is rationally inevitable thanks to backward induction from the last to the first round of the game. Accordingly, long-term participation in the market becomes a signal of the concept of the’shadow of the future’, suggesting that expected future interactions influence present behaviour.

In an environment where trust is in short supply, a pseudonymous actor’s track record is important if they want to operate on the dark web in the future. And most importantly, maintain a culture of vigilance within your organization by promoting cybersecurity awareness among employees through training programs and regular reminders. By following these best practices, you can create a safer digital environment for yourself and those around you, fostering a sense of belonging in this interconnected world.

Indeed, many empirical studies have confirmed Shapiro’s reputation theory 43, which states that a bad reputation negatively affects the price and number of sales of a product or service 20,44,45. In this context, the objective structure of social relations is partially shaped by comparing it to the previously described structure at the beginning of section two, in the absence of a reputation system. Reputation creates an incentive for cooperative behaviour and a disincentive for opportunistic behaviour. In addition, the trustor’s uncertainty is reduced since the trustor can control the trustee’s past behaviour.



