
Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web.
How Much Is Stolen Data Sold For On Darknet Markets?
This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement. The use of digital signatures can also help verify the authenticity of users and transactions. The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors.
OSCP Bootcamp In Pune Master Offensive Security With Hands-On Train

The cost can be exorbitant, but for victims, it’s always higher and devastating. For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of. In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone.
The Escrow Process
Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web.
Darknet Websites Uncovered
- The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web.
- A curated collection of darknet resources for educational purposes, offering insights into darknet frameworks, tools, and security practices.
- The platform supports Monero (XMR), Bitcoin (BTC), and several others to hide identities.
- Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web.
- It encrypts your traffic at the entry node and changes your IP address.
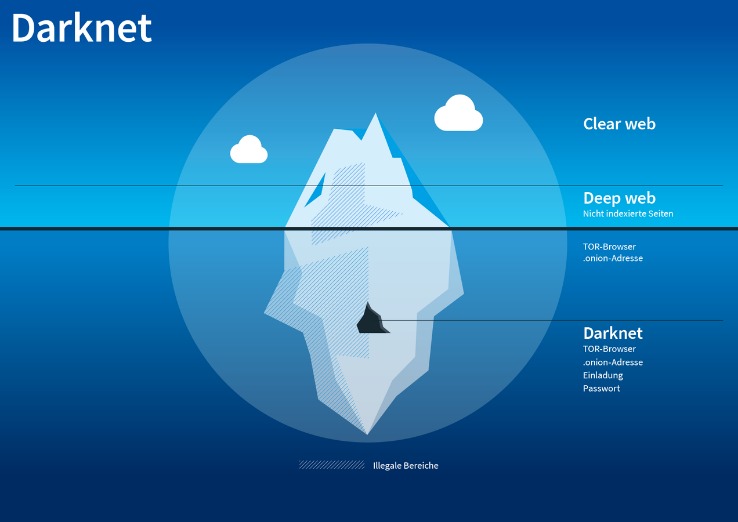
As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web).
The darknet markets keep on popping even when the authorities keep getting hard on them. While there are several darknet markets, each features unique characteristics tailored to various user needs. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.

Tor2door Darknet Market

If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s.
The Top 5 Dark Web Search Engines
The buyers, or “consumers,” are cybercriminals who use these tools to launch illegal activities. The victims, who are common users, businesses, and even banks, who end up paying the price. BidenCash was launched in 2022, and since it became a hot spot for cybercriminals to sell and buy illegal things, including stolen card information and personal data. However, in June 2025, BidenCash’s relevant domains (around 145) were seized by the US Department of Justice.
What Is Tails Software Used For?
Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices. Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease. To access the marketplace, dark web users must register first and pass the CAPTCHA test to prove they are human. The site allows users to find and buy a vast variety of products and services.
It allows you to buy and sell a wide range of products and services with a good user experience. This site supports PGP encryption and two-factor authentication features. Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds.
Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Following the NYT, the BBC launched a dark web “mirror” of their international edition in 2019. Note that some features of the normal website are not available on the .onion version, including BBC iPlayer. Archive.today is considered an important tool to track changes across government and corporate websites, preserve cultural heritage, and keep knowledge outside of autocrats’ reach.
Is It Illegal To Visit Onion Sites?
For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail.
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
Many dark web sites host illegal activities like gambling, drug trafficking, counterfeiting, cybercrime, and other illicit content. This includes the potential to pirate copyrighted material, which could also lead to legal consequences. Search engines are integral to the web browsing experience, but only about 10% of all websites are indexed on a typical search engine.



