However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets. Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. After that, many other marketplaces kept trying to take its place and become the top dark web market.
Exit Scams
- Therefore, all transactions involving the market have the market either as a source or as a destination node.
- Such models ensure that the market remains community-controlled and resilient to outside interference.
- A US grand jury has charged Iranian national Behrouz Parsarad for operating the Nemesis darknet marketplace, which between 2021 and 2024 facilitated the sale of illicit cyberservices and drugs.
- Sophisticated players shift operations, adopt new aliases, and resume business within weeks.
- This paired with the active introduction of crypto regulations, will sufficiently increase traceability of funds, aided even further through analytical tools like Crystal.
Most markets support alphanumeric only, but there are exceptions, one market’s username is automatically assigned by the system, and two markets have almost no restriction (i.e. any character including special characters). The minimum length of usernames is one character, but four characters is the most common minimum requirement. The maximum length of usernames is sometimes set at 16 or 20 characters, but half of the markets in our study had no length limit (i.e. we achieved successful registration with more than 64 characters). Special characters are mostly not supported, but underscore and dash are accepted in two markets. Most advocates of cryptocurrency viewed the arrest of the Silk Road founder as a positive development. After all, the immutable ledger in the Bitcoin blockchain had considerably aided law enforcement to track the illegal transactions of Silk Road.
Cyber-Attacks And Scams
Ransomware has continued to see revenues in the hundreds of millions of dollars, but a number of large, multilateral law enforcement disruptions coupled with decreased victim appetite to pay ransoms have made a dent in the ecosystem. 2024 has nonetheless been a productive year, as attack volume was relatively sustained and some ransomware groups have still managed to eke out payments — albeit in lower amounts. Below, we’ll take a closer look at three key trends that defined crypto crime in 2024 and will be important to watch going forward. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. Hydra also featured numerous vendors selling false identification documents.
Biggest Dark Web Marketplaces

Vendors often build up reputations through ratings and reviews, just like sellers on mainstream platforms. To reduce scams, many markets also use escrow systems, where the site holds the buyer’s payment until they confirm the item has been delivered. In fact, there are many more aggressive security tests we could have done, such as the rate limiting and the OWASP Top Ten.Footnote 7 But for ethical reasons, we figured we did not want to be a potential attacker.
- It claims to control more than 7,000 bots from 190+ countries, with data prices ranging from $3 to $10, based on the quality it offers.
- Smooth digital asset integration demands a well-considered strategy seasoned with innovation, regulation, and proactive risk management to make a secure financial future a reality.
- Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.
- Law enforcement agencies continue to focus their efforts on darknet marketplaces, particularly those involved in the trade of illicit substances.
- Blockchain intelligence firm TRM Labs reports that Abacus shutting down so abruptly has all the indications of either an exit scam or a covert law enforcement operation dismantling the activity.
Cryptojacking exploits victims’ devices for unauthorized cryptocurrency mining, leading to performance issues and financial losses. Fake wallets mimic legitimate apps, tricking users into depositing funds or revealing private keys. Fraudulent exchanges lure investors with promises of high returns or low fees before stealing their money. The rise of Ransomware-as-a-Service (RaaS) has further escalated cyber extortion, allowing criminals to execute attacks without technical expertise. Cryptocurrencies, especially Bitcoin and Monero, are commonly used for ransom payments due to their pseudonymity and global reach.
Market Operations
Actually, CAPTCHAs could also have a somewhat protective effect on DDoS (which we describe in Sect. 4.1.4). Initially, we tried to use an existing crawler to obtain (sales-related) data for all markets. However, we encountered some difficulties, which also shows the dynamic nature of most market security mechanisms.
Explicit And Illegal Content
We are only able to cover the end-user side of security mechanisms, which may not be comprehensive. But we also raise ethical considerations for academics on how to properly and ethically improve research in this area. In addition, and somewhat surprisingly, in our experience the use of I2P makes data collection easier. Tor’s network performance can cause the market server to take significantly longer to respond than over the I2P network. When considering data collection, the crawler’s downloader will require additional time to wait for the data to be downloaded locally 20.
24 Account Kill-switch
Both works find out that the business models of these markets is maturing. Wang et al. 34 compared Chinese and Occidental dark web markets, covering briefly some aspects of the security mechanisms they employ. During the heights of the COVID-19 pandemic, in 2020, Bracci et al. 6 analysed COVID-19-related products over a period of approximately eleven months.
This is often the reason why it is challenging to conduct large-scale longitudinal studies in dark web markets. Furthermore, Campobasso and Allodi 8 proposed a trainable, scalable crawler tool that makes it possible for researchers without computer backgrounds to use their tool for data collection in underground forums. In the experiments conducted by the authors, they overcame some restrictions (e.g., rate limiting, page loading time) by using different strategies when crawling different websites. It is both interesting and extra challenging that they also noticed a new and complex anti-crawling measure in the study, consisting on the dynamic obfuscation within HTML attributes (like IDs or the name of tags/classes).
To outpace criminals, continuous innovation in AI-driven analytics and forensic tools is necessary, ensuring real-time monitoring and intervention. Indeed, one of the most recent darknet market busts was the Nemesis online market. The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) specifically cited the market’s role in the fentanyl trade as a reason for the bust. On-chain data from BitInfoCharts shows that the daily number of monero transactions has halved from this time last year. For each entity, we keep track of the cumulative values of the six features for each transaction performed by the entity over time.
Sophisticated players shift operations, adopt new aliases, and resume business within weeks. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more.
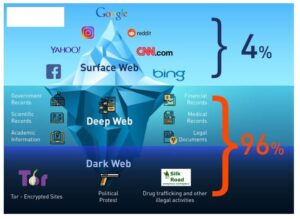
Over the years, dozens of large DNMs have been established and eventually shut down by law enforcement, including AlphaBay, Dream Market, Wall Street, and, most recently, Hydra. These geopolitical dynamics intensify the complexity of cybercrime, creating multi-layered threats that affect both public and private sectors globally. Decentralized autonomous organizations (DAOs) even govern some of these markets. Such models ensure that the market remains community-controlled and resilient to outside interference. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
At publishing time there is no indication that Abacus has been taken down by law enforcement but this scenario is not to be ruled out yet. Moreover, we argue that cracking (or knowing) rate limiting thresholds is more valuable, even if this requires some upfront experimentation. We can obtain complete data faster by using multiple threads to run the crawler simultaneously. Nevertheless, very aggressive rate limiting settings can also affect access by real customers. We wonder if we can design a crawler that can use an adaptive method to adjust the request rate dynamically instead of a set of predetermined values or a range of values. For some security experts, this could be considered surprising, insofar as Parsarad would likely have needed help to operate a marketplace the size of Nemesis.

In our current work, we focus on security mechanisms using more recent and broad data points. The insights and experiences we share are mostly regarding data collection. The takedown of Archetyp Market is a clear signal that law enforcement agencies, supported by advanced blockchain intelligence, can disrupt even the most entrenched illicit platforms. But the resilience and evolution of these networks underscore the need for continued cross-border collaboration, technical innovation, and real-time monitoring to stay ahead of the next generation of darknet threats.