However, don’t get scared of this frightening concept than the actual meaning of the dark web. In this article, we will extensively talk about the dark web, how to access it safely, how it differs from other parts of the web, and more. Dark web websites don’t bear Internet Corporation for Assigned Names and Numbers (ICANN) domains, such as .com.
Are Dark Web Browsers Safe?
Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. The technology behind this anonymous connection is known as “onion routing,” which utilizes a layered approach to obscure data and protect users’ locations on the network. Connecting to the Tor network might raise eyebrows depending on who and where you are. Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages.
How To Access The Dark Web On Your Device
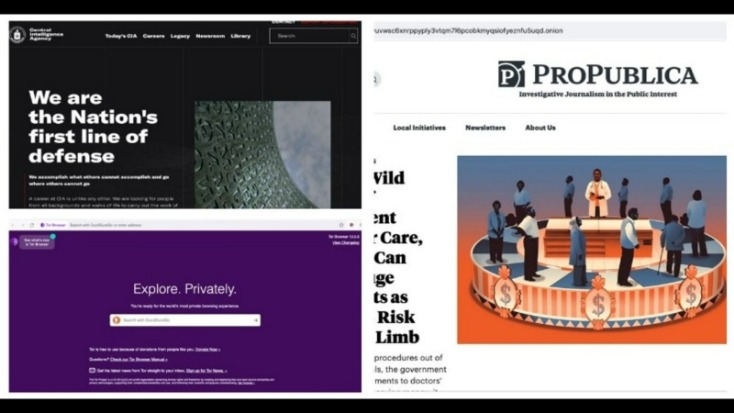
Tor Browser is pre-configured with privacy settings optimized for secure browsing, so you can enjoy a higher level of anonymity right from the start. It is essential to understand that while the dark web may harbor illicit activities, it is not representative of the internet as a whole. The vast majority of online content and services exist on the surface web, and the dark web represents only a small portion of the internet. You can access the dark web on mobile with a dedicated dark web browser app. Install a mobile dark web browsing app — like Tor browser for Android or the Onion browser for iPhone — and enter an onion URL to start browsing. The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people).
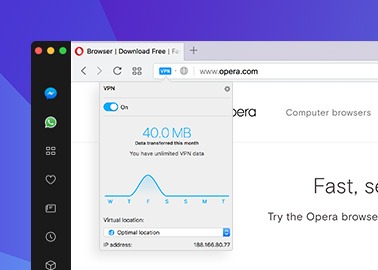
Download And Connect A VPN
KEY TAKEAWAYS Tor does provide some level of protection, but it will never provide enough data encry… KEY TAKEAWAYS If you’re in a hurry to find out the disposable email service provider, have a q… The RAT allows its creator to hijack your webcam and spy on you through your device’s camera lens.
Using Brave Browser (with Tor)
Setting up a virtual machine with a VPN and Tor can help you securely browse the dark web. The VPN and Tor ensure security, and the virtual machine will protect your device and other personal data from online threats like malware or hack attacks. This means that your VPN provider does not view your actual IP address, maintaining complete anonymity because the VPN protects you from malicious exit nodes. Unfortunately, your ISP can see you are on Tor, which may restrict your connection. However, Tor over VPN does not protect your device from dangerous Tor exit nodes.
Don’t: Click Suspicious Links Or Partake In Criminal Activity
If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code. If your device is unprotected, you could be a victim of malware or a hacking attack. If you’re intrigued and want a firsthand experience, follow this guide to learn how to access the deep web with an anonymizing browser. We’ll use the Tor browser for this guide, but any other browser that supports the Tor protocol will do.
How To Access The Dark Web
Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. Tails is a mere 1.3 GB download, so on most connections it will download quickly. You can install it on any USB stick that has at least 8 GB of space. Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web.
Many of these Reddits have rules prohibiting linking to illegal sites and services, so you likely won’t find anything illegal there. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions. ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users.
The button above leads you to its website where you can claim an exclusive 70% discount for the 2-year plan. Click the button, get the provider for around $3.3/mo, and install it on your device. NordVPN works on every Tor-friendly system – Windows, Android, Linux, and macOS. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information.
This setup provides a layer of anonymity and security, which is both its allure and its risk. Tor offers a level of privacy and anonymity by routing your internet traffic through multiple servers, making it challenging for third parties to trace your online activities. However, it is not foolproof, and users should still exercise caution when using Tor. In addition to standard websites, there are also servers that are only accessible through the Tor browser. Standard search engines do not list these domains in their results, so you need to know them in advance to connect to them. Many major companies have reserved .onion domains and host websites there, and there is a list of onion services on Wikipedia.
If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. Dark web marketplaces offer a range of both legal and illicit goods. Here’s a look at several of the illegal items you can buy — with prices — courtesy of Privacy Affairs’s Dark Web Price Index 2023.
- If your incoming traffic passes through a node run by cybercriminals, they could inject malware into the response code.
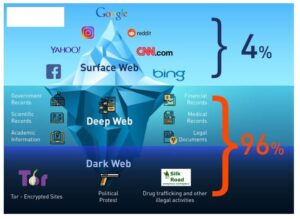
- It’s like an iceberg – The visible tip above water, known as the “surface web” represents the familiar, searchable content.
- It encrypts your connection and masks your IP address, providing an additional layer of protection against potential threats.
- You’ll notice that some websites’ loading times are longer when using Tor.
- There are marketplaces where people can sell stolen credit card numbers, conduct illegal drug transactions, and scam people out of their cash and crypto.
It’s essential to follow these guidelines to protect yourself and your personal information when exploring the depths of the internet. When you use Tor, which routes your internet traffic through many different relay nodes, your online activity is obscured because you’re browsing anonymously. The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet.
- Tor is a network designed to route traffic through multiple servers.
- We will discuss the setup procedure, ensuring security and anonymity, and offer tips for navigating the dark web safely.
- Each time you want to use it, you won’t have to download it on your device; instead, you can insert the DVD or the USB flash drive and use the OS.
- If you need to protect or enhance your streaming, gaming, or torrenting activities, a Virtual Private Network (VPN) is a much better option as a secure connection to the net.
- But as a result, Tor Browser will feel much slower than a normal web browser.
We’ve compiled a detailed guide to help you explore the Top Darknet Markets. Discover the most trusted platforms like Anubis Market, and more, complete with their unique features and security measures. Download the Linux version from torproject.org, extract the file, and run the start-tor-browser script. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions. These secure communication platforms improve your security when using Tor. Practice safe, smart digital habits if you must use Tor to log into personal accounts.
If you don’t remain vigilant and practice caution, many services you curiously investigate might be scams profiting off willing customers. A virtual machine is a file that behaves like your computer while virtually borrowing a dedicated amount of CPU storage and memory from it. It runs in a different environment and is partitioned from the rest of the host system. Therefore, activities within the virtual machine in no way impact your computer.