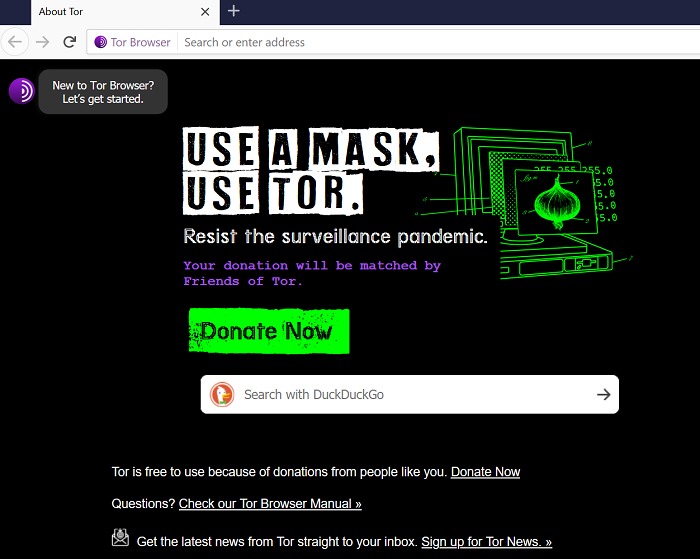
Likewise, some websites allow Tor, but with frequent Captchas that can be annoying. You can use a VPN if you’re in a country that restricts or heavily monitors Tor usage. You can also use it if you don’t want your network administrator or ISP to be aware of your Tor usage. However, if you don’t fall into these categories, or are a high-risk internet user (e.g., an investigative journalist or whistleblower), combining a VPN with Tor might be unnecessary. You can also use DuckDuckGo to find onion sites across the Tor network.
Can You Use The Tor Browser On A Mobile Device?
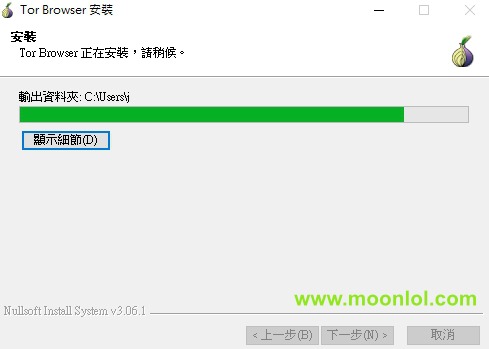
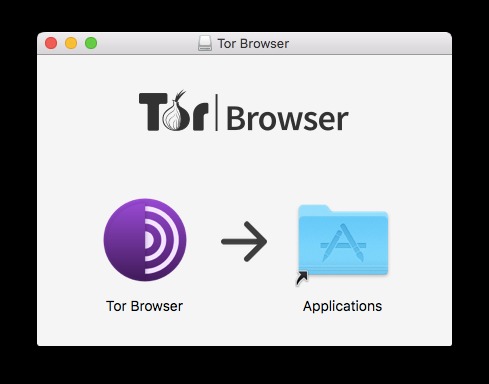
While the Tor Browser and the Onion Network are an excellent way to protect your online privacy and anonymity, it is by no means a perfect solution, and it has a few weaknesses. Go to the directory where you downloaded the Tor Browser installation file. Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been extracted, double-click on “Tor Browser Setup” to install the browser.
Go to the directory where you saved the downloaded Tor Browser installation file. Choose your language and click “OK.” Follow the installation prompts. There are four nodes between your computer and the website you want to connect to. In this comprehensive guide, I will endeavor to answer those questions and many more.
If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Damir is the team leader, product manager, and editor at Metaverse Post, covering topics such as AI/ML, AGI, LLMs, Metaverse, and Web3-related fields. His articles attract a massive audience of over a million users every month.
Quick Comparison Table: The Dark Web Search Engine Features
Just keep in mind it might take a bit longer to connect to a site due to Tor’s slow speeds. Also, like other privacy-focused tools, it might not be able to handle high-bandwidth activities because of slower network speeds. DNS leaks and malware threats are less likely to happen with this setup. However, its complicated setup and system needs might not make it ideal for casual users or people who aren’t very good with computers. Since most dark web browsers rely on the TOR network, the TOR browser will be the ultimate pick for deep browsing.
How To Use Tor Browser Safely
If registration is required for any service on the dark web, consider using burner accounts with no connection to your real identity. Despite these methods, finding reliable and safe onion links remains a significant challenge. The decentralized and often unregulated nature of the dark web means that there is no central authority vetting websites or ensuring their legitimacy. Many links found online may be outdated, leading to defunct services. Others may intentionally be misleading, directing users to scam sites, phishing pages designed to steal information, or even websites hosting malicious software.
Step 6: Access The Tor Browser On Tails OS
These services look at your IP address and guesstimate your country and language, but when using Tor, you will often appear to be in a physical location halfway around the world. The Tor Project offers Tor Browser for macOS, Windows, and Linux, as well as Android. From a macOS or Windows desktop, navigate via web browser to the Tor Browser download page and select the version for your operating system.
Conclusion: Access The Dark Web Safely And Responsibly
The freedom to communicate, publish, and read anonymously is a prerequisite for freedom of expression online, and thus a prerequisite for democracy today. Using and supporting Tor helps support freedom of expression around the world. Technically sophisticated users are encouraged to donate bandwidth to the Tor network by running a relay. As a result, don’t be surprised if Google or another service greets you in a foreign tongue.
How To Install Red Hat Enterprise Linux (RHEL) 9 ? RHEL
These links containing said random characters and numbers are hard to verify as legitimate or safe. While this should go without saying, many links pose as legitimate, and you may unknowingly click and invite harm to yourself. Once the configuration is complete, click “Connect” to open the Tor browser. You can toggle the settings that determine which browser automatically connects whenever you launch the program. Discover the easiest steps to install the Tor browser on any device.
Protecting your digital identity is crucial when navigating the dark web. Password managers and anonymous email services prevent unauthorized access and ensure private communications. Selecting the right browser for accessing the dark web is crucial, as it significantly impacts anonymity, security, and overall usability. Here’s a detailed analysis of the top browsers available in 2025, each uniquely suited to different types of users and requirements. Governments worldwide have intensified online surveillance in the name of national security, while corporations increasingly monetize personal data. As digital rights erode, anonymity online is becoming a necessity rather than a luxury for many individuals.
Best 10 Dark Web Browsers For Anonymous Deep Web Surfing
It’s easy to use, has intuitive design, and has a no-log policy so you don’t have to worry about your data being kept. I2P is the acronym for the Invisible Internet Project that permits you to access the internet without a hassle both on the dark web and surface web via a layered stream. It makes it pretty challenging to identify or locate you as this constant stream of data masks your information. With the help of this I2P browser, you can utilize both the private and public keys. It also implements the darknet technology and a decentralized file storage system for helping its users remain anonymous, just the way Bitcoin (BTC) works. However, it is a bit complicated, but the web anonymizing browser does the job.
- Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website.
- Whonix is so powerful that even malware that has root privileges will not be able to track down users’ IP addresses thanks to the TOR connections.
- Choosing the right browser and supporting tools depends on individual needs, technical proficiency, and specific privacy objectives.
- Install Norton VPN to help you access content and safeguard the data you share.
- Let’s find your key to safe access to the best dark web sites and anonymous browsing.
Google Warns About 97 Zero-Day Vulnerabilities Exploited In 2024
If you must use one, ensure it’s a VPN with a strict, independently audited no-logs policy. To use a new circuit, click the circuit button next to the domain. Then, click on New Tor circuit for this site, as illustrated below.