However, if you don’t fall into these categories, or are a high-risk internet user (e.g., an investigative journalist or whistleblower), combining a VPN with Tor might be unnecessary. However, the most secure way to use Tor is via .onion sites, which are built exclusively for the Tor network. Not Evil is a dark web search engine specifically designed for “.onion” sites. True to its name, Not Evil distinguishes itself by not employing advertising or web tracking. As a non-profit operation, Not Evil relies on a community of volunteers to identify and report false results and “abusive” sites, contributing to the integrity of its dark web search results. DuckDuckGo, known for its privacy-focused approach on the surface web, also has a presence on the dark web.
Legitimate organizations and companies also sometimes establish a presence on the dark web. Law enforcement agencies monitor the dark web for stolen data and criminal activity, while major media organizations track whistleblowing sites for news. One of the most frequently recommended security measures is to use a Virtual Private Network (VPN) in conjunction with Tor Browser, a practice often referred to as “Tor over VPN”. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. A VPN encrypts this initial connection, making it more difficult for the ISP to detect Tor usage. Some VPN providers offer “Onion over VPN” features, which route traffic through the VPN’s servers and then into the Tor network, providing a convenient way to access onion sites.
Many of these Reddits have rules prohibiting linking to illegal sites and services, so you likely won’t find anything illegal there. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web. Darknet markets facilitate transactions for illegal goods and services.
VirusTotal Explained How To Scan Files And URLs For Malware Using 70
You can check out this guide on the best antivirus software applications today. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites.
No Protection Against Malware
The safest and best dark web browsing tool for Android users is the official Tor Browser APK from the Tor Project site. Not just Tor alone, there are official sites for downloading every similar web browser APK. Always ensure you get your Tor browser or any other software directly from verified sources only, not from third-party sites. In your browser settings (like the NoScript extension in Tor), you will want to disable JavaScript and other active scripts.
Threat Of Malware

Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble. This can lead to incrimination for other activities later in life. China, for example, uses the “Great Firewall” to restrict access to popular sites and prevent citizens from evading government restrictions. This guide tells you all there is to know about the darknet and how to access both the deep web and dark web safely. Tor’s mission is to advance human rights with free and open-source technology, empowering users to defend against mass surveillance and internet censorship. We hate that there are some people who use Tor for nefarious purposes, and we condemn the misuse and exploitation of our technology for criminal activity.
- Users can take further steps to maximize privacy when browsing with Tor.
- Install Norton 360 Deluxe to help secure your device, block scams, and stay private online.
- Our experience has shown that this is the #1 way of doing things without risking your privacy.
- Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down.
- Most websites have HTTP and HTTPS versions, but connecting to the former introduces a security vulnerability.
Is It Illegal To Enter The Dark Web?
DuckDuckGo does not track your search history or collect personal data, making it a strong privacy-preserving option for searching both the surface and dark web. It doesn’t use the Tor network, so it’s not ideal for accessing the dark web, but it’s perfect for anyone looking to maintain strong privacy without needing to configure a thing. Freenet isn’t just an anonymity tool—it’s practically a digital manifesto. This peer-to-peer (P2P) platform encrypts data before sharing it and operates on a fully decentralized and distributed network.
What Is Best: Tor On Linux, Tor On Windows, Or Tor In Tails?
However, you can browse forums, watch videos, and chat with other people just fine. The dark web can be dangerous due to the presence of scams, cybercriminals, and malware. Users should exercise caution and follow safety practices to minimize risks.
Enhancing Your Security
Accessing blocked content can result in being placed on a watch list or imprisonment. Law enforcers can use custom software to infiltrate the dark web and analyze activities. You could be monitored closely even if you are not doing anything illegal.
He previously reported from Colombia for four years, where he wrote travel guidebooks to Latin America, and speaks Spanish fluently with a hilarious gringo-Colombian accent. He holds a Masters degree in Information and Cybersecurity (MICS) from UC Berkeley. Such hacking techniques ought to concern everyone, as innocent Tor users will inevitably get caught up in such fishing expeditions. The most successful technique to de-anonymize Tor Browser users has been to hack them.

The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet. However, this feature is only available on iOS, Android, and Windows. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely.
After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. You can use the Smart Location feature for the fastest connections.
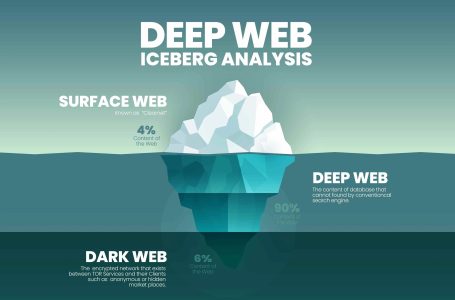
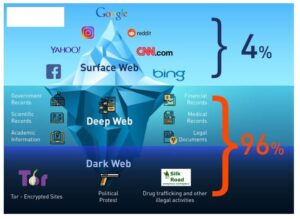
Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. Broadly speaking, any internet browser can access the dark web with a few modifications. Brave is easier to set up, though, and is already more privacy-oriented than most browsers.
- Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims.
- For this reason, you cannot browse through these sites using your default search engine.
- The story hints at why taking dark web safety measures is essential, even if you are jumping into the dark side of the internet only because of some curiosity.
- Use directories like The Hidden Wiki or Dark.fail, which list verified and regularly updated onion links.
- Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page.
Install The Tor Browser
Tor Over VPN is when you first connect your computer or mobile device to your VPN service and then use the Tor Browser to travel the internet. When you install the Tor Browser, it comes preconfigured with the most secure privacy settings. That means Javascript is disabled, extensions are disabled, and the browser is configured to warn you if an attempt is made to download a file and open it in another application.