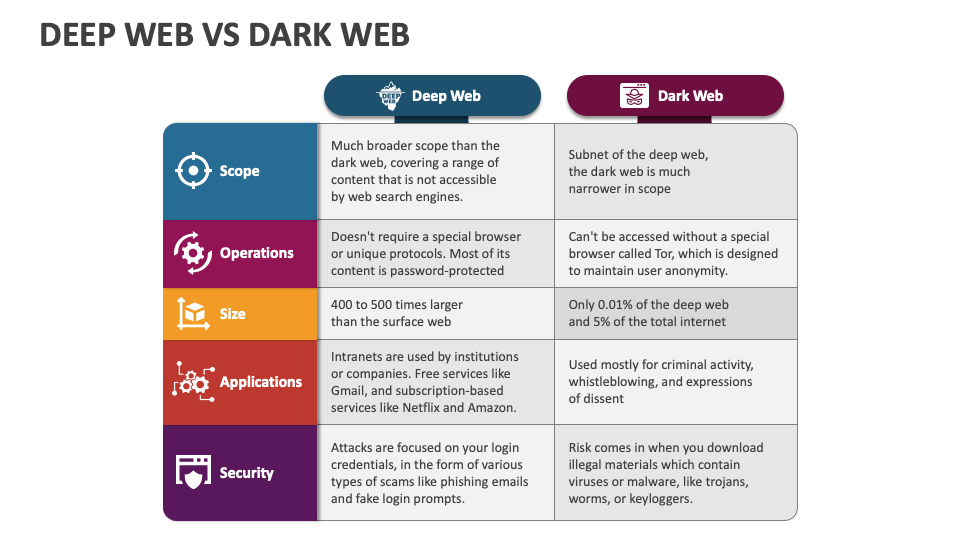
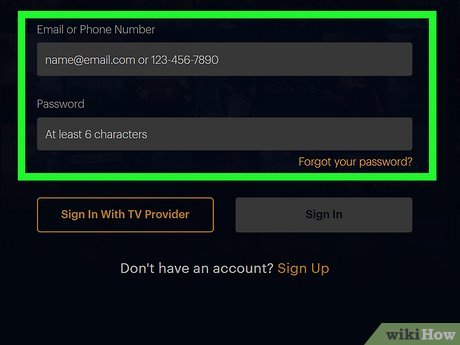
Web browsers can often access these pages with the correct credentials, but search engine crawlers cannot process them. For instance, the search engines won’t be able to access the servers and websites hosting data about some government-led secret alien mission. A private network, tagged as the deep web, can be right next to your house. It’s just the internet that isn’t within reach of standard search engine crawlers. For instance, the network maintained by some paid streaming service.
Get The Latest Insights, Trends And Security News Subscribe To CyberheistNews

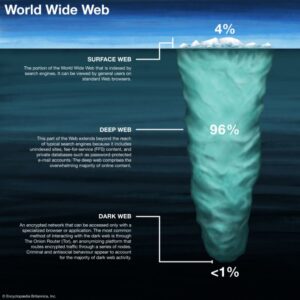
The site locations are encrypted onion links, and you need a special browser like Tor to access them. While the surface web is easily accessible through Google or other search engines, the Deep Web includes any content that requires special access. The Deep Web includes any online content that isn’t searchable through traditional search engines like Google or Bing. Unlike the public surface web, which is open to everyone, the Deep Web comprises information hidden from public access.
Deep Vs Dark Web: 17 Critical Differences
This architecture anonymizes users and complicates dark web monitoring. She combines her background in digital marketing from DePaul University with a passion for cybersecurity to create content that helps people and businesses stay secure. Her writing covers everything from password best practices to Privileged Access Management (PAM), with a focus on making technical topics easy to understand. There are several tools used for reaching these parts of the internet.

Why Do People Use The Deep Web?
- You can’t access the deep web or dark web using standard search engines like Google, because neither is indexed.
- Thus, while the dark web carries significant risks, it also highlights complex issues related to privacy and expression in the digital landscape.
- Companies need to update their threat prevention techniques to monitor dark web environments.
- On the other hand, accessing the dark web requires special software, most commonly Tor, which masks your identity and provides access to websites with .onion extensions.
- It turns out that a majority of cybercriminals, selling everything from compromised personal and financial data to drugs and hacking tools, constitute over half of Dark Web contents.
The architecture of the dark web features some key elements that make it an anonymous sanctuary for censured activities. In the CrowdStrike 2024 Threat Hunting Report, CrowdStrike unveils the latest tactics of 245+ modern adversaries and shows how these adversaries continue to evolve and emulate legitimate user behavior. To browse the dark web, you need to take preemptive steps toward anonymity.
More Private Data Will Be Sold
The deep web is essentially the unindexed portion of the web that search engines cannot access. The dark web is the hidden part of the internet that can only be accessed via specific tools like Tor (The Onion Router) or I2P (Invisible Internet Project). These tools anonymize user traffic by routing it through multiple encrypted nodes, making it difficult to trace identities or locations.
Potential Risks
Surfing the dark web could cause you to access dangerous websites or illegal content. However, while the internet includes a lot of data we don’t usually see (deep web), the dark web has a reputation for concealing and facilitating criminal activities. One of the most significant barriers to finding deep and dark web sources is that you must use the exact URL to access sources that are not indexed — even with a browser like Tor. For example, to access the popular dark web forum CryptBB, you must know the exact onion link; conducting a web search for the forum will not turn up anything useful. Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site.
How To Safely Access The Deep Web
Forums hosted on the Dark Web host discussions on successful and ongoing cyberattacks, newly discovered vulnerabilities, and other details of cyberattacks. Dark Web users also use the platform to exchange tips and tools for performing different cyberattacks and fraudulent activities. CrowdStrike Falcon® Adversary Intelligence provides comprehensive monitoring of the deep and dark web to identify threats targeting an organization’s brand, employees, and data. It helps detect compromised credentials, block fraudulent domains, and protect against phishing, brand impersonation, and cyber threats. It comprises many legitimate resources including academic databases, medical records, and private corporate networks. However, it is reasonable to know your content and ensure proper authorization.
We’ll quickly define the dark and deep webs before getting into different monitoring approaches for security teams. This study examines the evolution of dark web usage, highlighting the surge in activity during the COVID-19 pandemic. Beginner directories like The Hidden Wiki offer a starting point, but extreme caution is advised—many sites listed may be outdated, broken, or link to illegal content. It’s essential to avoid clicking anything blindly and to combine Tor with good security practices, such as keeping your device updated and never revealing personal information. The legal issues arise not from the access, but from the activities conducted within these hidden networks. For example, browsing a whistleblower platform or reading censored news through a Tor mirror site is lawful in many places and can even serve democratic and journalistic interests.
It’s Hard To Access: False
The dark web is a part of the deep web, but not everything on the deep web is part of the dark web. This wikiHow article teaches you the differences between the deep web, dark web, and surface web, as well as how to access each. In short, the Deep Web is simply the private part of the internet, where you need to log in to access information. Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
Prioritizing internet safety—utilizing encryption, employing secure passwords, practicing cautious engagement—can significantly reduce experiences of danger in both the deep and dark webs. As digital landscapes continue to evolve, so too must our commitment to understanding and navigating these complexities safely. Google, Bing, Yahoo, and all major search engines have bots that update their internet registries regularly whenever anything gets published on the internet. They index new entries and then show them for the relevant search queries made by the end users (us). However, the Dark Web isn’t all bad, and, in fact, the technology that makes it possible, Tor, was originally created by the U.S. government for legitimate purposes. The Surface Web, which is accessible via search engines like Google and Bing, only makes up a small portion of the Internet.
This anonymity can be achieved in various ways, but most of the sites on the dark web are “onion” sites. They can only be accessed using Tor Browser, which gives users access to the Tor network. The Tor network was created to allow completely anonymous (with some additional precautions ) communication over the internet. When a user and a website send data to each other over Tor, the data packets are randomly routed through a massive network of volunteer computers. Each of these nodes only knows where the packet just came from and where it’s going next, as each layer of an encryption onion is stripped from the packet contents. It’s only when the packet reaches the final destination that the last layer of encryption is removed and the intended recipient gets the original data.
The dark web hosts all kinds of illegal activities, many of which are the buying and selling of firearms, drugs, counterfeit money, fake passports, and stolen accounts. Tor and other onion routers like I2P, Freenet and Subgraph OS aren’t the only way to mask your identity online, but they are the most comprehensive. Internet users familiar with encryption and cybersecurity likely know about VPNs, which can also mask your IP, but only to a certain point. Ultimately, the responsibility lies with individuals to govern their online conduct wisely.
How CrowdStrike Protects You From Illegal Dark Web Activity
It is important to use strong, unique credentials for every account. Further, monitoring exchanges on dark web forums allows security personnel to gather threat intelligence. This enables them to gain insights into the operations of sophisticated adversaries and be warned of emerging threats. Most internet users access the deep web almost every time they are online.
This is both good and bad, and is why criminal activty is so widespread on it. Many worldwide concerns have arisen from it, one of the most notable being the infamous Silk Road—which is a marketplace for obtaining all sorts of goods. The surface web is also called visible web, or Indexed Web is the web that we use on a day-to-day basis. It is where our daily online activities take place, and what most people consider as the Internet. The dark web is the traditional place for threat actors to engage in cybercrime through selling stolen credentials, sharing guides for techniques, posting ransomware victims’ information, and more. Visiting a dark web site requires specialized software like the Tor Browser, which routes traffic through a series of random relays across the globe to mask both origin and destination.