If you can’t think of a strong password, consider using a password generator. Google and other companies can also help you generate strong passwords when you sign up on a website and store them in your profile. Anytime you visit that website again and need to log in, Google will pull that password from your list of passwords and auto-insert it. Earlier, we explained that the deep web is 400 times bigger than the surface web, but most people may not understand how big that is. The world’s most popular search engine, Google, has over 50 billion web pages in its index.
Do I Need A VPN For The Deep Web?
- Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
- Called “dark” because it is accessible with anonymity and only through certain networks and software such as Tor, this part of the Internet represents a small fraction of the overall Web.
- Accessing the deep web is quite straightforward, provided you know where you’re going and have the key (your credentials) to gain entry.
- However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces.
- Moreover, some websites generate content dynamically in response to user queries.
- You should consider using data breach monitoring tools to regularly check if your personal information has been leaked onto the dark web.
Obviously not all Tor users, but you never know whether someone might be looking into you. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. The dark web is a decentralized web, which means that the data is stored on many different servers around the world.
Use A Secondary Non-admin Account
The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information.
How Do You Access Content On The Deep Web?
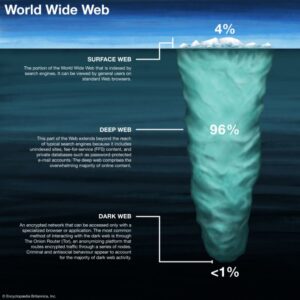
Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg. At the dark end of the web, you’ll find the more hazardous content and activity. Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser.
TORWatch
Deep web communication tools offer encrypted and anonymous channels for messaging, file sharing, and collaboration, enhancing privacy and security for users. Many activities we do online have a deep web component; however, the term “deep web” needs further understanding. Many people use it interchangeably with “dark web,” which is a common mistake. Corporate intranets on the Deep Web facilitate communication, collaboration, and data sharing within organizations. These systems are designed to be secure and inaccessible to the general public.
Deep Web: Unveiling The Hidden Layers Of The Internet
The purpose was to protect U.S. army soldiers and agents in the field, but also politicians who held secret meetings and conversations, which contained the highest security measures. The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones.
How To Find New, Active Dark Web Links
The Deep Web constitutes a multifaceted realm on the Internet that evades detection and accessibility through conventional channels such as popular search engines or major web browsers. Its content remains beyond reach due to either partial indexing by search engines or the imposition of password protection measures. While the deep and dark web offer undeniable benefits, users must navigate them responsibly. Misuse, such as accessing illicit content or engaging in unlawful activities, undermines the value of these platforms.

It’s safe to say that both these numbers grew exponentially in these 20 years of technological development. There’s also an increased chance of downloading malware, leaking credentials due to a phishing scam, or falling victim to financial fraud due to the lack of oversight. Accessing the Deep Web generally involves fewer risks compared to the Dark Web, but there are still some considerations.

Often, these parts of the Web are accessible only if you use special browser software that helps to peel away the onion-like layers of the dark Web. Private databases can be as simple as a few photos shared between friends on Dropbox. They also include financial transactions made on major sites like PayPal. The key feature of private databases is that people wish to share it with just certain people or preserve this information without having it publicly accessible to everyone. Fee-for-service sites are another major source of deep web content. Although fee-for-service sites, such as Netflix, are visible on the web, most of their content is not.

For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. In case you’re wondering how to access the deep web, chances are you already use it daily. The term “deep web” refers to all web pages that that are unidentifiable by search engines.
Therefore, you can prevent this exploitation by setting up a non-admin account. If you are in a position to report the incident safely, you should report it to the authorities immediately. It’s recommended not to be too vigilant here and leave the investigation to the professionals.
Access To Specialized Content:
VPNs are also used for accessing geo-locked content hosted by streaming services. The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data. ZDNET’s recommendations are based on many hours of testing, research, and comparison shopping. We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions.
The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. The deep web and dark web have many uses, but they also come with risks. If you know anything about data privacy and protecting yourself from identity theft, it’s easy to mitigate these risks on the deep web. In fact, you probably already do it whenever you log in to a secured website.
A VPN can help disguise your use of Tor and your visits to dark web resources. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more. ExpressVPN is our pick for the best VPN overall, thanks to its fast and reliable connection and the wide range of platforms it works on. However, remaining anonymous can be invaluable to protesters, civil rights groups, journalists, lawyers, and other vulnerable groups.
For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. For example, you can only find your Facebook friends, photos, and other information by logging into your Facebook account and finding the information there. On the deep web, you can find such “private” information on web pages. It’s the last part of an internet domain name, stated after the last dot. For example, Google.com and PixelPrivacy.com both belong to the “.com” top-level domain. So, even though it does exist on the internet, Google doesn’t index any of these pages or content.