You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Our rigorous research and testing have revealed revealing truths and busted myths. We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety. In August 2021, co‑founder “DeSnake” relaunched AlphaBay with a decentralized infrastructure and stricter vendor vetting. As of early 2025 the reboot remains online, though it commands a fraction of its former traffic and faces constant DDoS attacks and phishing clones. A cautious setup minimizes the chances of leaking your identity or infecting your device.
In this comprehensive guide, I will endeavor to answer those questions and many more. I’ll go into how the Tor system works, explain the Onion Network, what a relay is, and how to make the Tor Browser work best to protect your online privacy and anonymity. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android. A VPN will mask your location and stop the online breadcrumbs that can lead back to you. Connections made while a VPN is active will also be encrypted, helping you stay protected from eavesdropping and man-in-the-middle attacks.
Exploring The Use Cases Of Darknets & Dark Markets
Once you have those, there are several ways to tunnel through the dark web. This multi-layered redirection ensures your actions leave no trace, offering a high level of anonymity. If you’re planning to return, consider creating a burner OS or using a hardened Linux distro like Tails. These tools leave no trace on your device and reduce your exposure even if something goes wrong. Never install extensions or additional add-ons, even if they seem useful. They change your browser fingerprint and make you easier to track.
What Do People Sell Or Exchange On Darknet Markets?
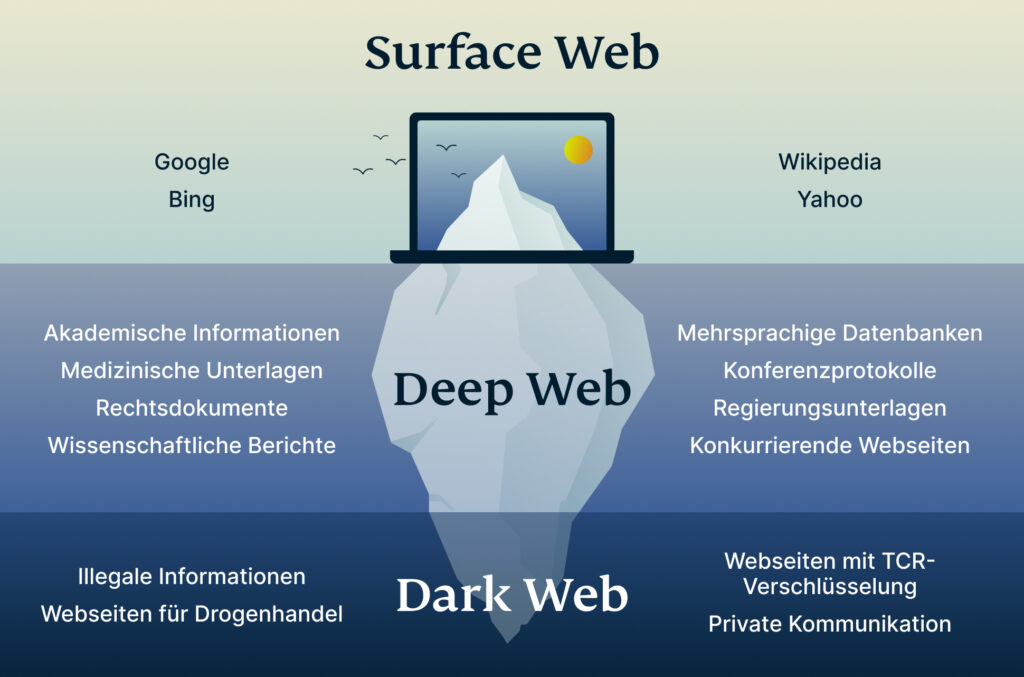
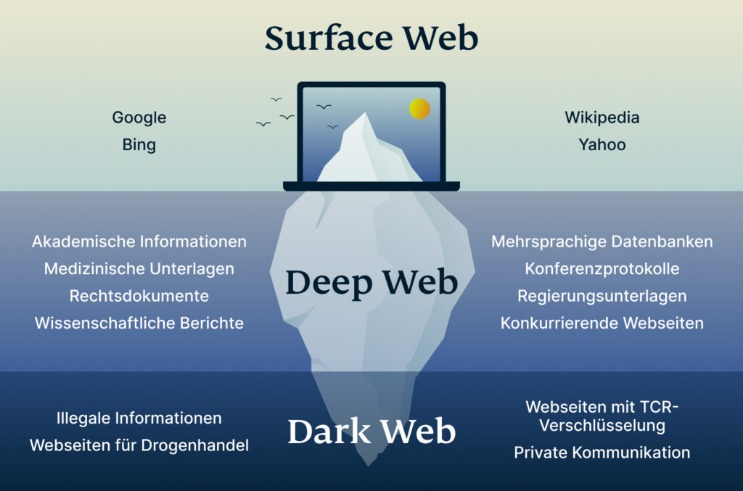
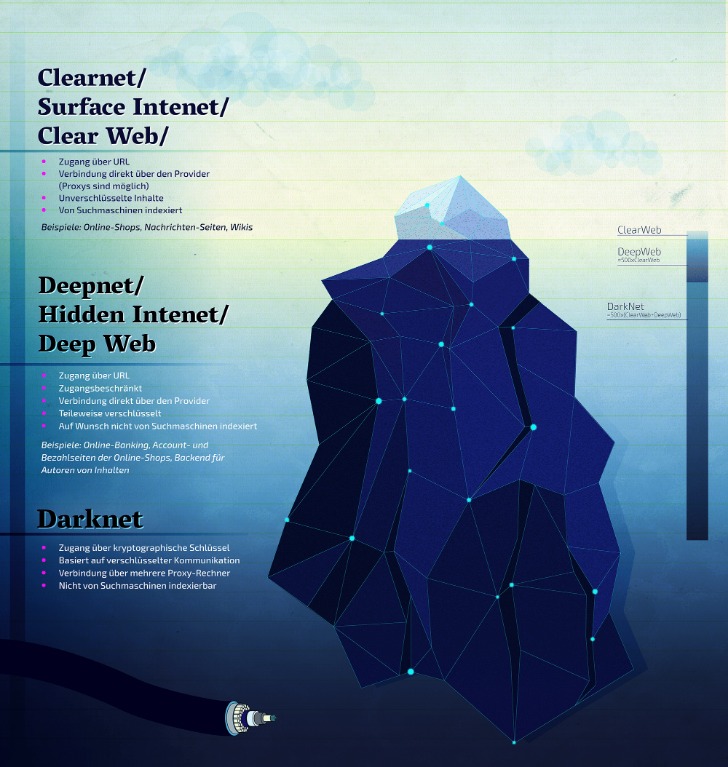
- Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity.
- However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credits card, and more.
- Focusing on privacy and security, MGM supports transactions in Bitcoin (BTC) and Monero (XMR), and utilizes a direct payment system for each purchase, appealing to users who value privacy.
- This market specialized in selling marijuana related products and magic mushrooms, with no “hard drugs” for sale.
- These pages rely on the same protocols and domain names as the public Internet, yet search‑engine crawlers cannot reach them because authentication gates keep casual visitors out.
That means that only 0.024% of all the known pages are findable in Google’s search engine. The users only have access to a fraction of the available data and web pages. The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo.
Staying Up To Date With Darknet Markets
You can access it today using specialized browsers and software. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve. By the mid-2000s, the dark web emerged as a sub-environment marked by specialized websites that utilized the “.onion” domain, making them accessible only through Tor.
Q: How Do I Access TOR?
LifeLock notifies you if we find your personal information on the dark web, and we’ll help you run damage control with assistance from legal experts and recovery specialists. There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data. Learn more about the kinds of sites that can be found on the dark web and how you can access them. Then, try LifeLock free for 30 days to help find out if your personal data is leaked on the dark web. By using Tor over VPN, the VPN encrypts your data and hides your IP address. This means that all of your traffic, including your Tor Browser activity, is protected.
Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
Tor Browser is available for Windows, Linux, Mac OS, and Android. For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable.

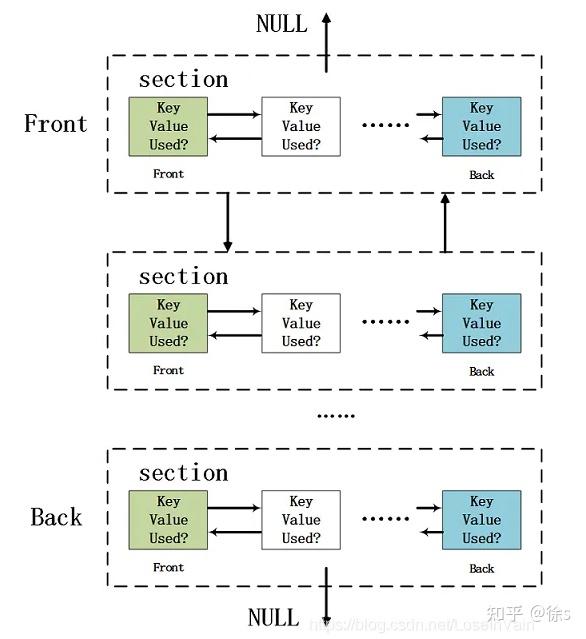
The encrypted data is sent through a series of network-based nodes called onion routers. While strong encryption, VPNs, proxy servers, and hidden web addresses can all contribute to a more anonymized experience, there is no singular system available that is completely private and secure. If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app.

Exiting Safely
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
This means you can use your favorite browser instead of the Tor Browser and still benefit from being routed through the Onion Network. While there are numerous VPN services that work well with Tor, I’ve found that NordVPN offers the best protection and compatibility, and keeps your personal information safe. This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities. A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded.
Why Do You Need A VPN To Access The Dark Web?
If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report. However, it is often prohibited for ISPs to sell your data to third parties. During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data. So, if you aspire to use Tor privately, you can use VPN or Tor gateways (Tor nodes that are not publicly indexed). Tor Bridges or a VPN will help you to use Tor privately, as your ISP (Internet Service Provider) will not see that you’re connected to a Tor node.
Hacking And Cybercrime Sites
This high-security level makes the Tor browser fit for opening ‘onion’ links (dark web links), which use onion routing with several layers of encryption to protect your online traffic. The browser itself bounces web requests over three servers while encrypting the data before the request gets to the intended server. Most darknet market administrators are now tightening access controls. Every potential participant’s credentials must be vigorously vetted before they can join.



