The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. If you know the right websites, you can easily access a tremendous amount of information, including research articles, news stories, and more. Yes, you can still be tracked on the dark web despite its privacy features.
Is It Illegal To Visit Websites On The Dark Web?
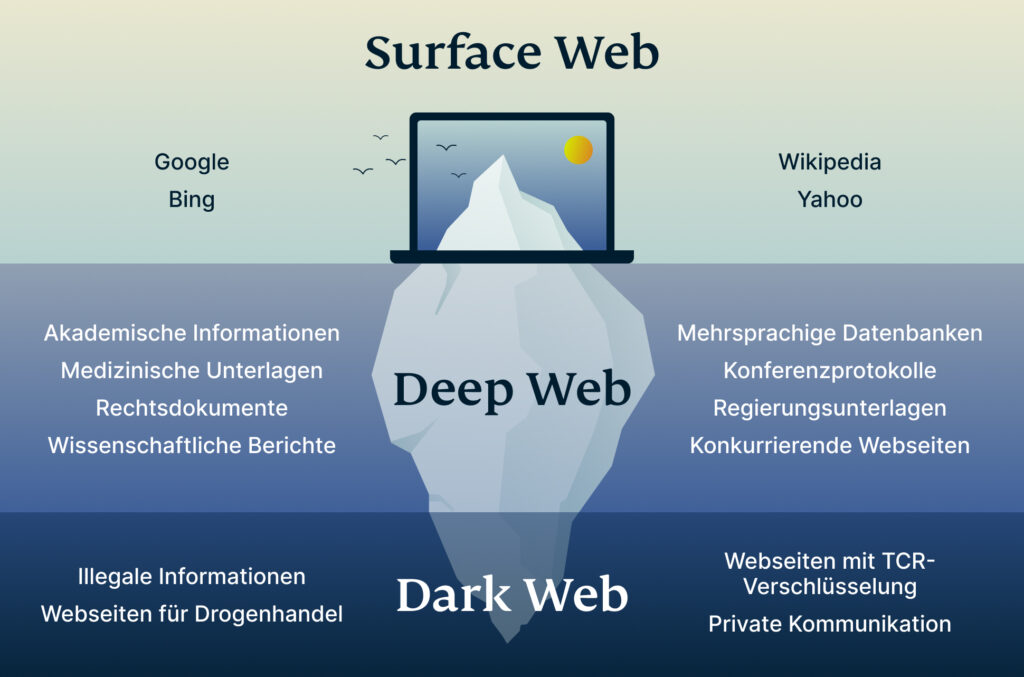
That’s why we took the guessing work out of it for you, and made this list of the best dark web sites you should check out. It’s a hidden collective of sites that you could only access through a special browser. Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. The prevalence of scams and malware forced many darknet users to treat the Hidden Wiki cautiously, cross-referencing links with trusted community forums or using verified mirrors only.
- Kazakhstan criminalizes “distribution of information facilitating drug trafficking,” which prosecutors have applied to forum posts linking to .onion addresses.
- You can also use it on the surface web, but it is still unadvisable without proper safety measures.
- The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites.
- No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
- Confidential government files and pages tied to unlawful trafficking often get filtered out.
- Although the site is still continually expanding and improving, it has become a significant resource on the Tor network.
Yes, governments can still monitor onion sites if they really want to. Local offices frequently monitor suspicious activities that involve their jurisdictions, so authorities might be closer to your anonymous communication than you know. ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network.

Avoid Pluggable Transports Carelessly
Darknets also serve as a platform for whistleblowers and privacy advocates. Platforms like SecureDrop enable individuals to submit documents and communicate securely with journalists, thereby exposing corruption and wrongdoings while preserving their anonymity. The significance is in safeguarding the right to free speech and the role of the press as watchdogs. Businesses should be aware of the potential for data leaks and invest in data loss prevention measures. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures. As one marketplace is taken down, another often rises in its place.
Tor Opens The Gateway To The Darknet
The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs). While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes. For example, the network dn42 exists to help users form connections and networks rather than to preserve user anonymity. While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking.
Table Of Contents
Also, we’d like to point out that several dark net sites face technical issues and remain inoperative temporarily or shut down permanently. Although every site on this list works fine at the time of writing, we can’t guarantee the same for a later date. It lets anyone send and receive email anonymously via webmail or with an email client. ProPublica was one of the first major news outlets to launch a dark web version of its site back in 2016. Cyble plays a key role in this landscape, offering AI-powered threat intelligence and digital risk protection. As we enter 2025, these tools are adapting with improved security and functionality to meet user needs.
Dark Web Tools And Services
Today, the Hidden Wiki remains a prominent element on the dark web, continuously updated to adapt to the ever-changing technological landscape. If the Tor browser is running, you can immediately check whether it is working as intended. When you purchase through links in our articles, we may earn a small commission. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using. This handy feature monitors the dark web for signs that your login details or other personal info have been leaked. However, the dark web is so complex and vast that if law enforcement takes down one market, it pops up elsewhere.
The Hidden Wiki

SecureDrop has even been adopted by various news organizations worldwide. It provides a safe haven for anyone looking to shed light on wrongdoing or share critical information with the media. ZeroBin’s onion address ensures your traffic is routed through multiple nodes, so it’s challenging for any third party to trace any message back to your original location. ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy.
Do I Need A VPN If I Use Tor?
During my tests, ExpressVPN’s military-grade encryption and verified no-logs policy provided consistent protection against tracking and monitoring. The kill switch feature also ensures your real IP stays hidden if your connection drops. Facebook’s official dark web version helps users access the platform in countries where it’s blocked.
This is high-level protection; no one can intercept your data or activities. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.

These services form the communication backbone for sensitive conversations in high-risk environments. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures. You risk legal consequences if caught participating in illegal transactions.
- Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely.
- Facebook’s onion portal is an essential communication tool for people living under oppressive regimes, despite the social media giant’s controversial reputation when it comes to privacy.
- However, there are some significant variances in the background despite the similarities.
- Finally, consider visiting Onionland from a virtual machine to protect your actual PC from harm if you do manage to catch something nasty while trawling the depths.
- Given the regularity with which .onions sites go offline and disappear, the more directory sites you know about, the better.
- For real-time messaging, Ricochet Refresh offers decentralized, peer-to-peer encrypted chats over Tor without central servers, greatly reducing surveillance risks.
While the Tor Browser provides strong anonymity, using a VPN (Virtual Private Network) alongside it adds an extra layer of security and privacy. A VPN encrypts your internet traffic before it enters the Tor network, hiding your Tor usage from your internet service provider and shielding your IP address from the first Tor relay. This setup can help prevent network-level surveillance and reduce risks in environments where Tor use might be flagged or restricted. Choose a trustworthy VPN service that has a strict no-logs policy and supports connection without DNS leaks. Avoid free VPNs as they often lack adequate security or monetize user data.
D Onion Websites: Between Anonymity And Risks
Always remember to use a VPN in conjunction with the Tor browser for an additional layer of privacy. A VPN encrypts your internet traffic, making it extremely difficult for anyone to trace your online movements. Moreover, refrain from sharing any personal information while browsing the hidden wiki, as this can jeopardize your anonymity and security. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data.
All Onion sites use The Onion Router (Tor) protocol to encrypt the user’s connections. It’s only possible to access onion sites through the Tor browser or by setting up some special network configurations. Deutsche Welle (DW) is a German state funded news organization that reports on worldwide topics and events. In order to avoid censorship of their content, they’ve created a .onion site to ensure it’s accessible for all.



