Credit card details stolen from the US are among the cheapest globally due to high supply. Their average price in 2021 is $17, less than half the global average of $35. Credit cards, Paypal accounts, and fullz are the most popular types of stolen information traded on the dark web, but they’re far from the only data worth stealing. Sales of passports, driver’s licenses, frequent flyer miles, streaming accounts, dating profiles, social media accounts, bank accounts, and debit cards are also common, but not nearly as popular.

Personal Finance
On top of all that, they could make purchases or request money from contacts listed in the PayPal account. Hijacking a PayPal account requires a different approach than stealing a credit card number. Instead of card numbers and CVVs, criminals steal usernames and passwords that they’ve gathered either through phishing or malware. They can then sell the account credentials to a buyer who can log in and drains the funds, or the vendor can transfer the requested amount of money from the victim’s account to the buyer’s account.
Online Payments
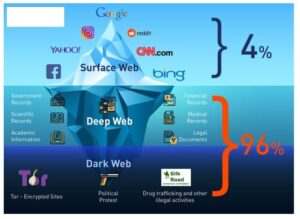
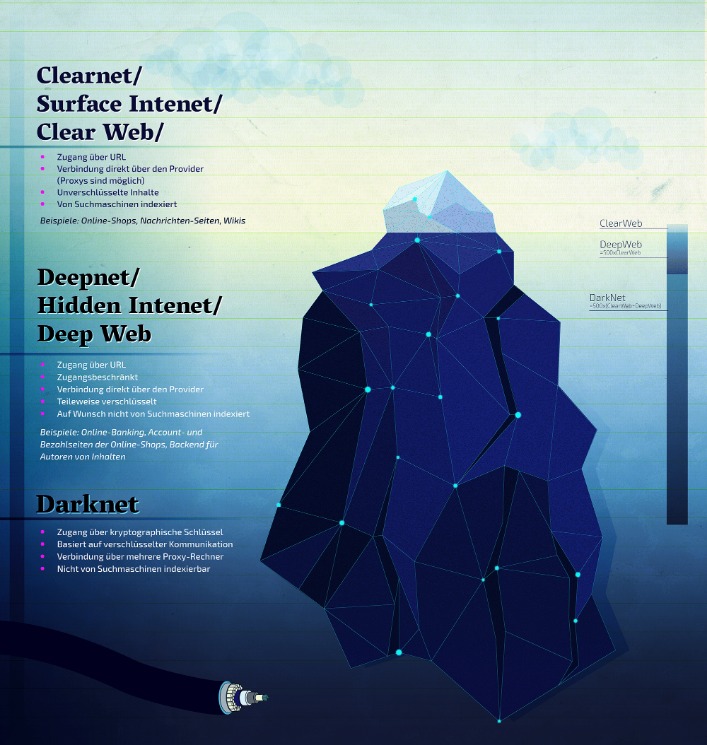
Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. The story of dark web marketplaces kicks off with Silk Road, launched in 2011. It was the first big site where people could anonymously buy drugs using Bitcoin, and it gained a lot of attention, until it was shut down by the FBI in 2013. Four of the five most popular brands in this category were conventional cryptocurrency exchanges, with only Paxful standing out as a peer-to-peer platform. Hacked VPN log-ins were disproportionately popular on Russian markets, which accounted for 43% of all VPN listings.
VPN Services
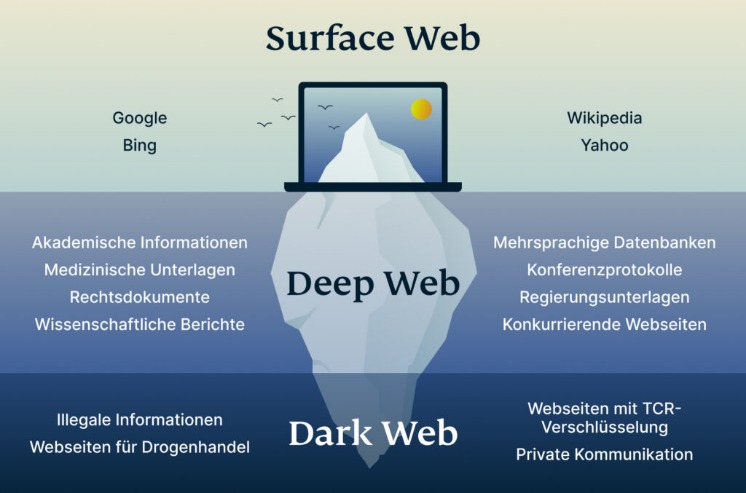
We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. As well as analyzing the trade in personal data on the dark web, we also investigated the sale of the tools used to steal these credentials. Our report on this topic was published in July 2018 and included data on U.S. and UK brands. The average person has dozens of accounts which form their online identity, all of which can be hacked and sold.
Security Leaders Share Thoughts On DaVita Data Breach
Get a personalized step-by-step Action Plan & ID Safety Score based on YOUR dark web hits. They also claim that while many of the leaked passwords appeared unique and “strong-looking,” a large portion were reused. Please logout and then login again, you will then be prompted to enter your display name. It’s always helpful to also have the best antivirus software installed on your devices and kept up to date. Social Security numbers and other national ID numbers are for sale on the dark web but aren’t particularly useful to cybercriminals on their own.
“There are likely only a handful of major credit card data farmers doing the majority of the data theft,” Armor says. “It appears these wholesalers are, directly or via a middleman, distributing the data and guidance on the most effective ways to sell it to retailers or salespeople that post advertisements to the underground markets and forums.” Stolen credit cards are either cashed out or used to make purchases that can be resold. Credential stuffing is a cyberattack that involves the use of credentials obtained from a data breach on one service to attempt to log into any related or unrelated service.
Ready To Explore Web Data At Scale?
Passport scans sell for only a fraction of the price due to their digital nature and the greater risk of not being accepted. We found that the financial barrier to entry for this kind of cybercrime to be alarmingly low, with powerful tools selling for pocket change. Scan your devices regularly using trusted software, such as Malwarebytes for Windows and macOS, and Avira Mobile Security for iOS and Android. It’s also well worth enabling real-time web protection too, even if you have to upgrade to the paid version to do so.
How Easy Is It To Use Compromised Data To Conduct Credential Stuffing Attacks?
Verified Stripe accounts with payment gateways are the most expensive, at $1,000. User accounts from online payment services such as Paypal or Western Union are at the top of the criminals’ list of priorities. However, some providers do not guarantee that the accounts for the financial services are actually accessible. The web is full of cheap bots hackers can easily use to automatically run compromised login details and match them with existing accounts on different platforms.
NordVPN was listed for sale over 80% more frequently than Windscribe, the next most popular VPN service. Windscribe was vastly more popular in Russia (10.5% of listings) than it was elsewhere (0.5%), most likely due to the fact that it remains one of the few VPN services with Russian servers. Almost half of the 20 most popular brands in the category offered a variety of courses across a range of disciplines. Four platforms were focused on access to books and book summaries, while three were language learning platforms. The three biggest markets for cryptocurrency account log-in details were Bohemia, Nemesis and Blacksprut, which were host to 49% of all such listings. The average price for the category was very high at over $152, compared to $112 for the payment platforms category.
Law Enforcement Action Had Little Effect On Supply And Prices
Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. The following table shows which categories of hacked account credentials were most popular on the Russian-language darknet markets. It shows the top 10 categories only, to see the full list download the data sheet. If we were to exclude data from Russian markets then PayPal would be tied with NordVPN as the most popular brand. More generally, payment services were highly prevalent, even with bank accounts and credit cards excluded. In response to our findings NordVPN noted that credential stuffing was a cyberattack in which credentials obtained from a data breach on one service are used to attempt to log into another, unrelated service, such as NordVPN.
Topics And Products Sold
People unexpectedly have their card cloned, their identities stolen, or their accounts hacked. Most stolen card details end up on the dark web marketplace for a quick profit, and this can happen before you even know about it. In addition to PayPal account balances, they can also transfer money from any connected bank accounts or credit cards.
It has a bidding feature, with new batches of stolen data being frequently added. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data.
Darknet Market Price Index: 2019 Mid-Year UK Update
- And then there’s malware—click the wrong link or download the wrong file, and your device could get infected.
- Japan, the UAE, and Europe have the most expensive identities at an average of $25.
- Haveibeenpwned.com should be your first port of call, as it’ll help you find out which of your email accounts and old passwords have been compromised in a data breach.
- Hulu was more popular than average on this darknet market, with more of its accounts for sale than any other streaming service.
- As a consequence of this, likely fewer crypto trading accounts and wallets were available for hackers to target.
These attacks rely on the actual physical swipes of cards, which then allow the malware to exfiltrate credit card data along with verification data such as a PIN numbers or zip codes. Most of use just have the standard personal account, but Premier and Business accounts also exist, and are up for sale on the dark web. But those tiers don’t have much influence on dark web prices, which are largely governed by account balance.
While these guidelines may appear complex and bothersome initially, they will become second nature once you become accustomed to them. This is when you will develop a crucial sense of cybersecurity both online and in everyday life. Malware can compromise systems running on various operating systems, including Microsoft Windows and Android. Once installed, it grants hackers full access to the machine’s capabilities.