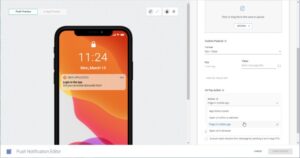
Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Be warned that this may cause some websites to not work properly. Now that you’ve completed the download, it’s time to install the Tor browser on your device. (The installation instructions that follow are for the macOS platform, I’ll mention where it’s different for Windows.) Simply double-click the downloaded file in your download folder.
Searching For A Hitman In The Deep Web
In addition, it also revisits already indexed sites to update discover and remove downed and offline sites. However, to maintain the servers, they offer the possibility of inserting advertising banners on their home page. Tor Search is a very efficient search engine because it indexes new content all day from the TOR network. That it is an open source project that is in charge of handling suggestions and comments anonymously. On the other hand, we have Tor2Web, which is a service that helps people who are not yet in the Tor network. The site started as a fork of the ahmia search engine, this will remain a central part of the site.
- Ulbrich will spend the rest of his life in prison for money laundering, computer hacking, and conspiracy to traffic narcotics.
- No user names are tied to actual identities, and no moderation like one may find on Reddit.
- We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch.
- Stick to tried-and-tested sites and do your best to avoid scams.
- Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
Darknet Markets
This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web. This solution focuses on identifying stolen data, brand misuse, and potential threats before they can cause significant harm. With Brandefense, businesses gain early visibility into risks that may otherwise remain undetected until it’s too late.
The More You Spend, The More Data You Get Per Credit Card Number
The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.
Safe Browsing Practices On The Hidden Wiki
However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
Hidden Answers
We couldn’t provide any context or updates to investigators or know if they had even notified the targets about the threat. He’d exploited a vulnerability in the site to gain access to the back end, and now, astonishingly, he could see everything that the site administrators could see. The details of who they wanted killed and how, with smiling photos of each target. And payments in bitcoin for the hits—many in the tens of thousands of dollars. Yes, but you need to be cautious because there are many malicious sites on the dark web.
The Following Addresses Are V2 Only (they Don’t Have V3 Addresses Yet):
Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A virtual private network (VPN) is a good way to mask Tor activities.
Since they’re willing to break laws, they already have lots of options available that provide better privacy than Tor provides. For example, if you attempt to connect to Facebook’s hidden service using Tor2web, Facebook blocks the connection and tells you it’s a bad idea. On Android phones and tablets, we previously recommended the Orbot proxy app or Orfox browser from Google Play.

Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection. This makes it even harder for third parties to see your email traffic.

It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client.
The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. Then, simply click the operating system that you are using and download the file. The site offers downloads for macOS, Windows, Linux, and Android. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store.
Are Onion Sites Safe?

The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily. When you search for something on Google or Bing, you’re using the clear web. Onion sites, and darknets in general, can host some horrifying content. A large amount of it is fictional, but there is no doubt you can end up viewing potentially damaging and compromising material if you are not careful.